Question: Consider applying the discrete-time epidemic model described in lecture) for infectious diseases to a computer worm. In this scenario, the potential victim population is
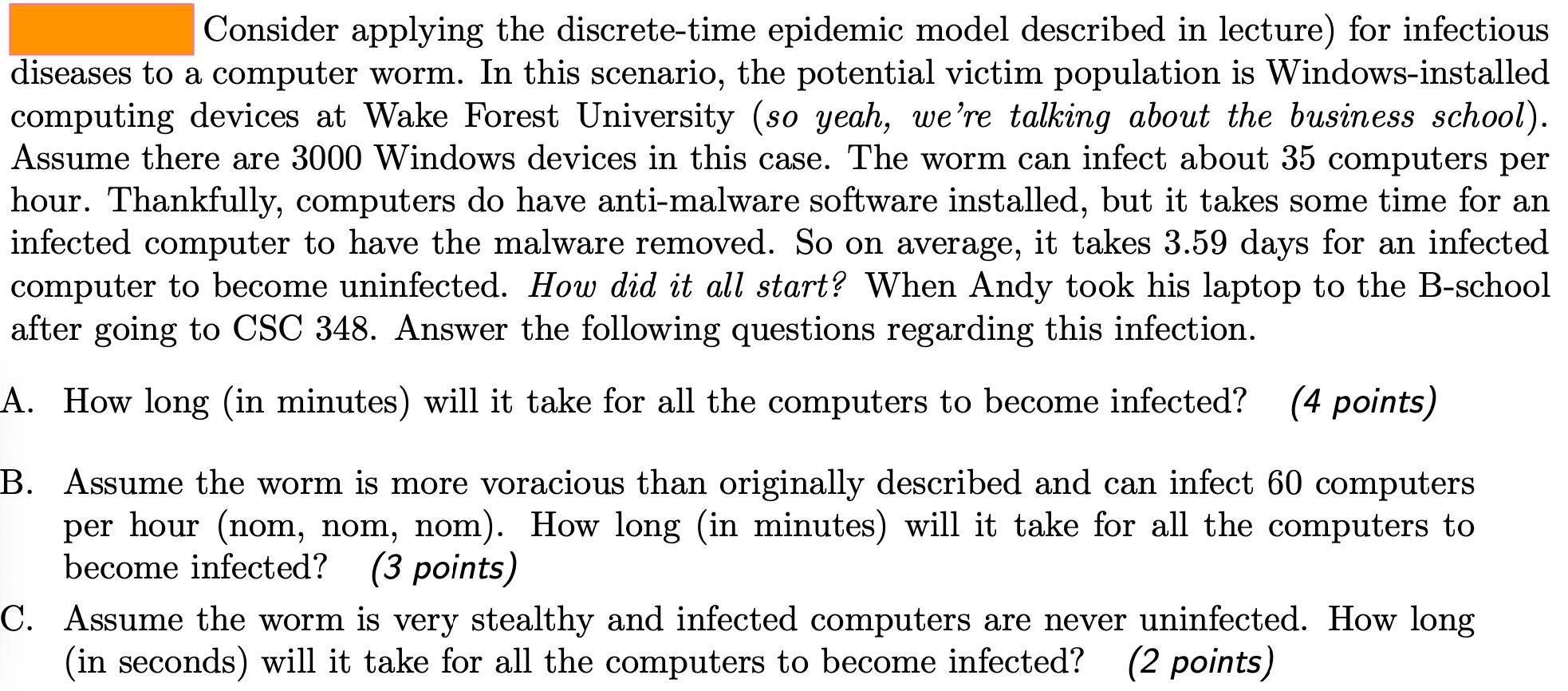
Consider applying the discrete-time epidemic model described in lecture) for infectious diseases to a computer worm. In this scenario, the potential victim population is Windows-installed computing devices at Wake Forest University (so yeah, we're talking about the business school). Assume there are 3000 Windows devices in this case. The worm can infect about 35 computers per hour. Thankfully, computers do have anti-malware software installed, but it takes some time for an infected computer to have the malware removed. So on average, it takes 3.59 days for an infected computer to become uninfected. How did it all start? When Andy took his laptop to the B-school after going to CSC 348. Answer the following questions regarding this infection. A. How long (in minutes) will it take for all the computers to become infected? (4 points) B. Assume the worm is more voracious than originally described and can infect 60 computers per hour (nom, nom, nom). How long (in minutes) will it take for all the computers to become infected? (3 points) C. Assume the worm is very stealthy and infected computers are never uninfected. How long (in seconds) will it take for all the computers to become infected? (2 points)
Step by Step Solution
3.33 Rating (153 Votes )
There are 3 Steps involved in it
QUESTION Consider applying the discretetime epidemic model described in lecture for infectious diseases to a computer worm In this scenaro the potential victim population is Windows installed computin... View full answer

Get step-by-step solutions from verified subject matter experts


