Question: Consider the following protocol: AKDC: KDC A: A B: B A: IDA || IDB|| N E(Ka, [Ks || IDB || N ||E(Kb, [Ks ||
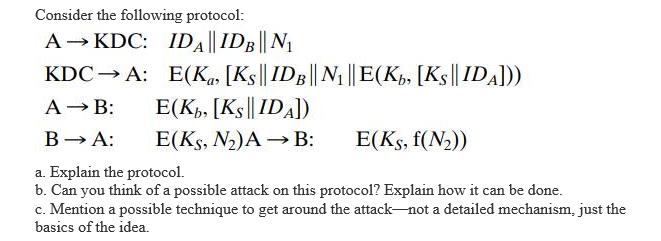
Consider the following protocol: AKDC: KDC A: A B: B A: IDA || IDB|| N E(Ka, [Ks || IDB || N ||E(Kb, [Ks || IDA])) E(Kb, [Ks||IDA]) E(KS, N)A B: E(Ks, f(N)) a. Explain the protocol. b. Can you think of a possible attack on this protocol? Explain how it can be done. c. Mention a possible technique to get around the attack-not a detailed mechanism, just the basics of the idea.
Step by Step Solution
3.49 Rating (169 Votes )
There are 3 Steps involved in it
The detailed answer for the above question is provided below Step 1 This is the Needham Shroedar Pro... View full answer

Get step-by-step solutions from verified subject matter experts


