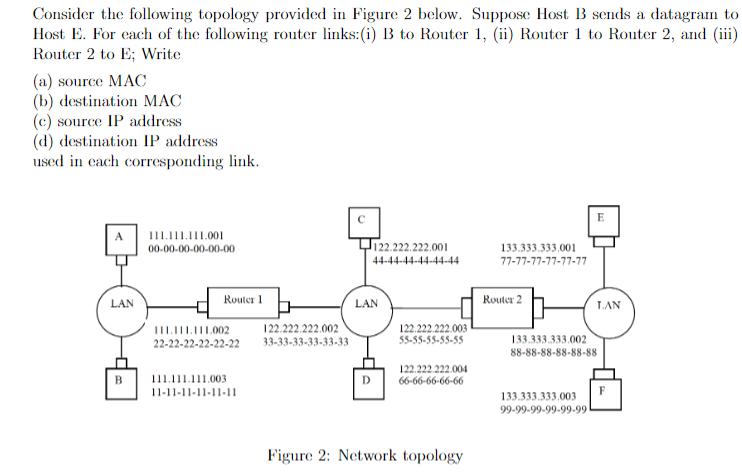
Consider the following topology provided in Figure 2 below. Suppose Host B sends a datagram to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Consider the following topology provided in Figure 2 below. Suppose Host B sends a datagram to Host E. For each of the following router links: (i) B to Router 1, (ii) Router 1 to Router 2, and (iii) Router 2 to E; Write (a) source MAC (b) destination MAC (c) source IP address (d) destination IP address used in each corresponding link. LAN 111.111.111.001 00-00-00-00-00-00 Router 1 111.111.111,002 122.222.222.002 22-22-22-22-22-22 33-33-33-33-33-33 111.111.111.003 11-11-11-11-11-11 122.222.222.001 44-44-44-44-44-44 LAN 122.222.222.003 55-55-55-55-55 122.222.222.004 D 66-66-66-66-66 Figure 2: Network topology 133.333.333,001 77-77-77-77-77-77 Router 2 TAN 133.333.333.002 88-88-88-88-88-88 133.333.333.003 99-99-99-99-99-99 F Consider the following topology provided in Figure 2 below. Suppose Host B sends a datagram to Host E. For each of the following router links: (i) B to Router 1, (ii) Router 1 to Router 2, and (iii) Router 2 to E; Write (a) source MAC (b) destination MAC (c) source IP address (d) destination IP address used in each corresponding link. LAN 111.111.111.001 00-00-00-00-00-00 Router 1 111.111.111,002 122.222.222.002 22-22-22-22-22-22 33-33-33-33-33-33 111.111.111.003 11-11-11-11-11-11 122.222.222.001 44-44-44-44-44-44 LAN 122.222.222.003 55-55-55-55-55 122.222.222.004 D 66-66-66-66-66 Figure 2: Network topology 133.333.333,001 77-77-77-77-77-77 Router 2 TAN 133.333.333.002 88-88-88-88-88-88 133.333.333.003 99-99-99-99-99-99 F
Expert Answer:
Answer rating: 100% (QA)
Network Address Translation NAT is a networking technology that authorizes numerous dev... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these computer network questions
-
Explain the concepts of database clustering and load balancing. Discuss how they improve performance and availability. Provide an example of configuring a database cluster.
-
IFRS and U.S. GAAP are relatively similar with respect to current liabilities and contingencies. Relatively minor differences relate to when financing must be in place for a liability expected to be...
-
Dickinson Company has $12,080,000 million in assets. Currently half of these assets are financed with long-term debt at 10.4 percent and half with common stock having a par value of $8. Ms. Park,...
-
ABC Company produces and sells I product. Once the products are produced, they are sold, and there is no work-in- process, no any inventory in stock. Company uses standard costing method in its...
-
Is a company ever too small to need to engage in human resource planning? Why or why not? Discuss whether you think Robert Reed planning his hiring strategy at an appropriate time in the firm's...
-
Sixty-year-old Wanda Davis retired from her computer consulting business in Boston and moved to Florida. There she met 27-year-old Ava Jain, who had just graduated from Eldon Community College with...
-
The trial balance for Silver Shovels Exploration Company does not balance. The following errors were detected: a. The cash balance is overstated by $3,000. b. Rent expense of \($390\) was erroneously...
-
Cellular telephone service has certainly become more important vis--vis wired telephone service over the past decade. Will this trend continue? How will the trend toward cellular service be affected...
-
12 13 Design a four-bar mechanism such that = 120, 03 = 160 and 12 = 70, 13 = 100. Input link rotates clockwise and output link also rotates clockwise. A length of fixed link is 5 cm.
-
WorldCom revealed that in addition to the US$3.8bn in expenses improperly recorded as capital, an internal audit discovered that US$3.3bn in profits were improperly recorded on its books from 1999 to...
-
Alanine and glutamine are the most abundant amino acids in humanblood plasma. Explain, in detail, why alanine and glutamine arepresent in much higher concentrations than any other amino acids inhuman...
-
Compare and contrast the labor relations practices between two different countries. Any surprises?
-
On December 31, Jarden Company's Allowance for Doubtful Accounts has an unadjusted credit balance of $15,500. Jarden prepares a schedule of its December 31 accounts receivable by age. Accounts...
-
In addressing the behavior of any of these staff members, is there anything you need to be cautious of from a legal or regulatory perspective?
-
Discuss how each step in the sales process relates to the AIDA (attention, interest, desire, action) ?
-
Joe Refresh Ltd. began with retained earning of $400,000. The company earned $150,000 during the year, and paid a dividend of $100,000. What is the ending retained earnings balance ?
-
The relationship between x, y and 2, given that p = is given by the equation where a= V1 (F) belongs to span( V1, V2) where and V2 x+ay+bz - C TUNA b = (9) 3 0 S and c =
-
The maximum pressure that can be developed for a certain fluid power cylinder is 15.0 MPa. Compute the required diameter for the piston if the cylinder must exert a force of 30 kN.
-
Consider the network fragment shown below. x has only two attached neighbors, wand y. w has a minimum-cost path to destination u (not shown) of 5, and y has a minimum-cost path to u of 6. The...
-
Because an integer in [0, 2/n - I] can be expressed as an n-bit binary number in a DHT, each key can be expressed as k =(k0' k1 . .. , k0_1,), and each peer idenn tifier can be expressed P =(p0' Pl'...
-
Suppose you are interested in detecting the number of hosts behind a NAT. You observe that the IP layer stamps an identification number sequentially on each IP packet. The identification number of...
-
How does electronic commerce differ from EDI? What are the implications of these differences to the control and auditability of a company?
-
A company involved in e-commerce would expect a firewall to do all of the following except: a. Intercept traffic that meets specific criteria and send the traffic back to the originator of the...
-
To obtain evidence that user identification and password control procedures are functioning as designed, an auditor would most likely a. Attempt to sign onto the system using invalid user...

Study smarter with the SolutionInn App


