Question: Consider the Merge-Sort (M-S) algorithm presented in class. Give a permutation of the input list (1, 2, 3, 4, 5, 6, 7) that will
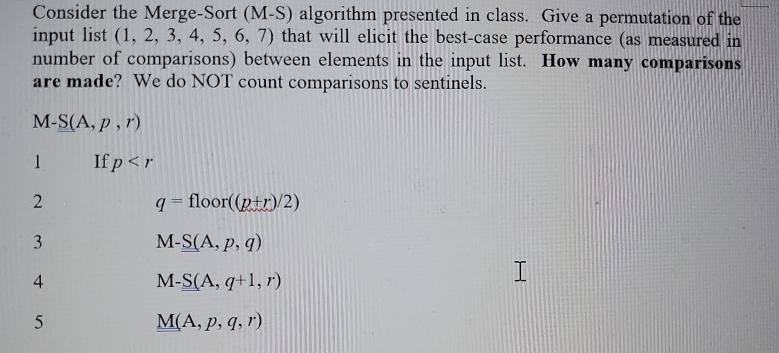
Consider the Merge-Sort (M-S) algorithm presented in class. Give a permutation of the input list (1, 2, 3, 4, 5, 6, 7) that will elicit the best-case performance (as measured in number of comparisons) between elements in the input list. How many comparisons are made? We do NOT count comparisons to sentinels. M-S(A, p, r) 1 2 3 4 5 If p
Step by Step Solution
3.35 Rating (155 Votes )
There are 3 Steps involved in it
In the MergeSort algorithm the bestcase scenario occurs when the input list is already sorted In thi... View full answer

Get step-by-step solutions from verified subject matter experts


