Question: Convert each character in the input string to its opposite case, please use memory addresses to get each character of the input string. Q2:
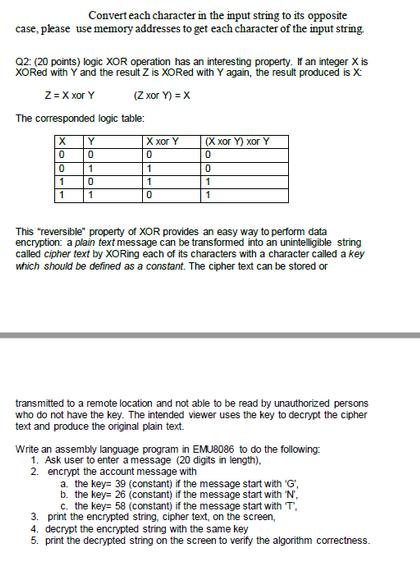
Convert each character in the input string to its opposite case, please use memory addresses to get each character of the input string. Q2: (20 points) logic XOR operation has an interesting property. If an integer X is XORed with Y and the result Z is XORed with Y again, the result produced is X: Z = X xor Y (Z xor Y) = X The corresponded logic table: X 0 0 1 1 Y 0 1 0 1 X xor Y 0 1 1 0 (X xor Y) xor Y 0 0 1 1 This "reversible" property of XOR provides an easy way to perform data encryption: a plain text message can be transformed into an unintelligible string called cipher text by XORing each of its characters with a character called a key which should be defined as a constant. The cipher text can be stored or transmitted to a remote location and not able to be read by unauthorized persons who do not have the key. The intended viewer uses the key to decrypt the cipher text and produce the original plain text. Write an assembly language program in EMU8086 to do the following: 1. Ask user to enter a message (20 digits in length). 2. encrypt the account message with a. the key 39 (constant) if the message start with 'G', b. the key= 26 (constant) if the message start with 'N'. c. the key 58 (constant) if the message start with T. 3. print the encrypted string, cipher text, on the screen, 4. decrypt the encrypted string with the same key 5. print the decrypted string on the screen to verify the algorithm correctness.
Step by Step Solution
3.46 Rating (149 Votes )
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


