Question: cryptography/security engineering Sig is a digital signature scheme. In particular, assume it is the RSA-based digital signature-with-appendix. Assume Bob knows the eneryption and digital signature
cryptography/security engineering 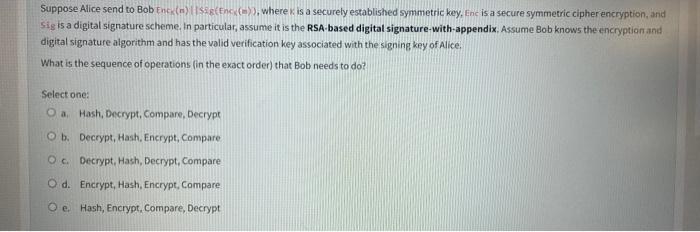
Sig is a digital signature scheme. In particular, assume it is the RSA-based digital signature-with-appendix. Assume Bob knows the eneryption and digital signature algorithm and has the valid verification key associated with the signing key of Alice. What is the sequence of operations (in the exact order) that Bob needs to do? Select one: a. Hash, Decrypt, Compare, Decrypt b. Decrypt, Hash, Encrypt, Compare c. Decrypt, Hash, Decrypt, Compare d. Encrypt, Hash, Encrypt, Compare e. Hash, Encrypt, Compare, Decrypt
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


