Question: subject- cryptography/security engineering Alice and Bob have securely established two symmetric keys K1 and K2. They have also agreed on the choice of ciphers. Suppose
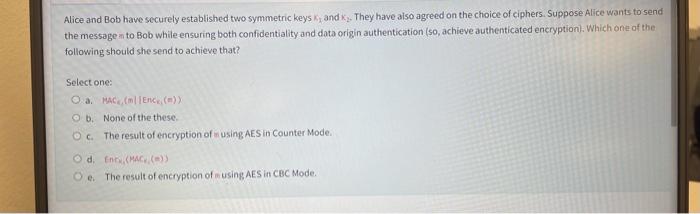
Alice and Bob have securely established two symmetric keys k1 and k2. They have aiso agreed on the choice of ciphers. Suppose Alice wants to send the messoge an to Bob while ensuring both confidentiality and data origin authentication (so, achieve authenticated encryption). Which one of the following should she send to achieve that? Select one: a. HAC4(mEnCi(m)) b. None of the these. c. The result of encryption of using AE.S in Counter Mode. d. Enci, MACi,(=)) e. The result of encryption of using AES in CBC Mode
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


