Design and configure routers and hosts (but switches) in the network by allocating each IP addresses...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
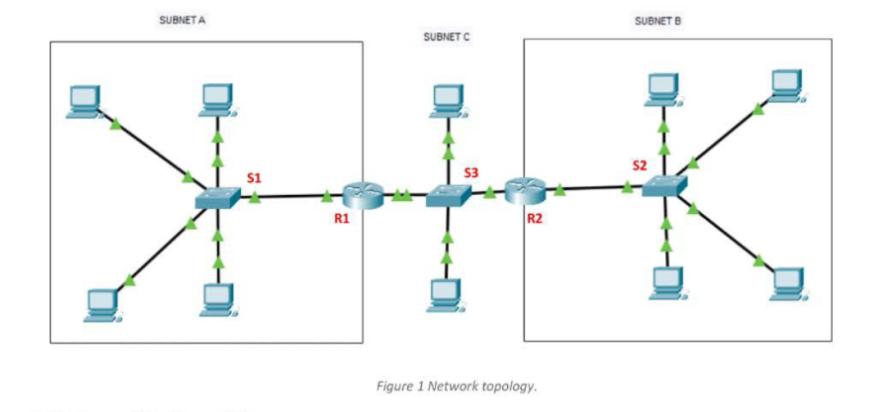
Design and configure routers and hosts (but switches) in the network by allocating each IP addresses in an appropriate and minimal range (to maximise the spare ranges for future use) as shown in Figure 1 using Packet Tracer, and verify the connectivity fully works across the network including inter and intra networks. Notes: 1. Use 'ping' to verify connectivity 'successful' status 2. Display names and IP addresses of devices and interfaces on the Packet Tracer screen 3. Use/design smallest subnet mask for each network where possible 4. Show the subnetting scheme in a single page in your presentation 5. Check 'no auto-summary' command, which will be required to configure routing protocol such as RIP and EIGRP Task 2 Layer 2 Implementation and Analysis In Subnet A, redesign and configure the network to allocate VLAN10 and VLAN 20 for 2 hosts by allocating each IP addresses in an appropriate range. Check connectivity within the same and different VLANs. Demonstrate how Layer 2 and Layer 3 work differently by enabling and disabling the R1 interface, and analyse the results and explain why it was a 'success' or 'failure'. Task 3 Layer 3 Evaluation In Subnet B, clear the ARP table of devices, and ping from a host in Subnet B to a host in Subnet C. Evaluate and analyse how Layer 2 and Layer 3 addresses (source and destination) are allocated in each network's ingress andctiv egress interfaces. For example, what address is and is not changed at the router interfaces with Subnet A and C? to Explain why and justify your answers. SUBNET A $1 R1 SUBNET C $3 R2 Figure 1 Network topology. SUBNET B 52 Design and configure routers and hosts (but switches) in the network by allocating each IP addresses in an appropriate and minimal range (to maximise the spare ranges for future use) as shown in Figure 1 using Packet Tracer, and verify the connectivity fully works across the network including inter and intra networks. Notes: 1. Use 'ping' to verify connectivity 'successful' status 2. Display names and IP addresses of devices and interfaces on the Packet Tracer screen 3. Use/design smallest subnet mask for each network where possible 4. Show the subnetting scheme in a single page in your presentation 5. Check 'no auto-summary' command, which will be required to configure routing protocol such as RIP and EIGRP Task 2 Layer 2 Implementation and Analysis In Subnet A, redesign and configure the network to allocate VLAN10 and VLAN 20 for 2 hosts by allocating each IP addresses in an appropriate range. Check connectivity within the same and different VLANs. Demonstrate how Layer 2 and Layer 3 work differently by enabling and disabling the R1 interface, and analyse the results and explain why it was a 'success' or 'failure'. Task 3 Layer 3 Evaluation In Subnet B, clear the ARP table of devices, and ping from a host in Subnet B to a host in Subnet C. Evaluate and analyse how Layer 2 and Layer 3 addresses (source and destination) are allocated in each network's ingress andctiv egress interfaces. For example, what address is and is not changed at the router interfaces with Subnet A and C? to Explain why and justify your answers. SUBNET A $1 R1 SUBNET C $3 R2 Figure 1 Network topology. SUBNET B 52
Expert Answer:
Answer rating: 100% (QA)
Topology R1 Routeren Routerconf t Enter configuration commands one per line End with CNTLZ Routercon... View the full answer

Related Book For 

Business Data Networks and Security
ISBN: 978-0134817125
11th Edition
Authors: Raymond R. Panko, Julia L. Panko
Posted Date:
Students also viewed these computer network questions
-
a) How are the building connections classified based on their moment-rotation characteristics? b) Determine the safe load P that can be carried by the joint shown in Figure. The bolts used are 20 mm...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
The value of a dirt bike decreases by 25% each year. If you purchased this dirt bike today for $500, to the nearest dollar how much would the bike be worth 5 years later?
-
A homogeneous wire is bent into the shape shown. Determine by direct integration the x coordinate of its centroid. 45 45
-
Calculate Financial Statement Ratios Using the chart below (which replicates portions of the: "10 Point Test" Ratios for Overland Park, KS in FY2015 on page 88 in Kyoko and Marlowe). In the Ten Point...
-
We continue our study of term life insurance demand from Chapters 3 and 4. Specifically, we examine the 2004 Survey of Consumer Finances (SCF), a nationally representative sample that contains...
-
The standard cost of Product B manufactured by TLC Company includes three units of direct materials at $5.00 per unit. During June, 28,000 units of direct materials are purchased at a cost of $4.70...
-
ME 4451 Lab 2 Handout RRR Serial Robot Servo Control
-
6.6, 7,000 lb/hr of aniline is to be heated from 100 to 150 by cooling 10,000 lb/hr of toluene with an initial temperature of 185F in 2- by 1-in. IPS double pipe hairpin exchangers 15 ft long....
-
fill in the gant chart below (until time 20) for the most feasible case (X, Y, or Z) 0 1 2 3 4 5 6 7 8 00 9 10 11 12 13 14 15 16 17 18 19 20
-
Why is it important for professionals to maintain adequate records?
-
What state of mind is required for intentional misrepresentation?
-
Under what conditions can a patient be said to have assumed the risk?
-
Most states have adopted some form of a(n) ____________ negligence standard.
-
Interspousal immunity and parent-child immunity were instituted a. to prevent a flood of litigation. b. out of a concern that allowing such suits would encourage family discord. c. out of a fear of...
-
The analyst wants to test the Fisher effect, the hypothesis suggested by Irving Fisher that nominal interest rates increase by 1 percentage point for every 1 percentage point increase in expected...
-
As indicated by mutual fund flows, investors tend to beat the market seek safety invest in last year's winner invest in last years loser
-
A client PC has two simultaneous connections to the same web-server application program on a web-server. (Yes, this is possible, and in fact, it is rather common.) What will be different between the...
-
a. Distinguish between Step 1 and Step 2 in the routing process. 10a1.) The first step in the routing process involves _________. a. Selecting the best match row b. Comparing the packet's destination...
-
a. What is the promise of P2P applications? 22a.) Which of the following is considered a bigger problem with traditional client/server based architectures than with peer-to-peer architectures? a....
-
Using tha data file usmacro, estimate the ARDL \((2,1)\) model Your estimates should agree with the results given in equation (9.42). Use these estimates to verify the forecast results given in Table...
-
Using the data file usmacro, estimate the \(\operatorname{AR}(1)\) model \(G_{t}=\alpha+\phi G_{t-1}+v_{t}\). From these estimates and those obtained in Exercise 9.16, use the results from Exercise...
-
Consider the \(\operatorname{ARDL}(p, q)\) equation and the data in the file usmacro. For \(p=2\) and \(q=1\), results from the LM test for serially correlated errors were reported in Table 9.6 for...

Study smarter with the SolutionInn App


