Question: do exercise 1 rer se SARAR How do you callanete, vera attack space for a bit R25. Explain bow biometric syviems ate weloverable to the
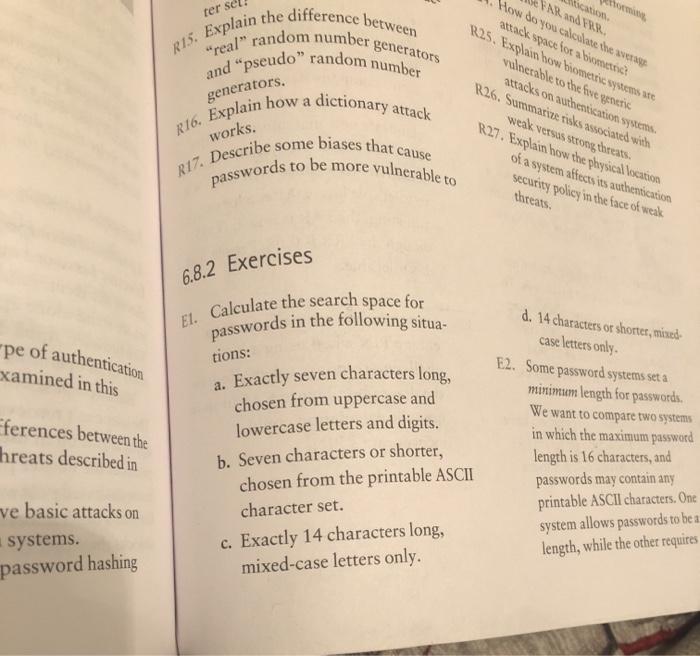
rer se SARAR How do you callanete, vera attack space for a bit R25. Explain bow biometric syviems ate weloverable to the fove generic attacks on authentication system R26. Summarize tisks associated with generators. dictionary attack works. weak versus strong threats R27. Explain how the physical location of a system affects its authentication security policy in the face of weak threats. to be more vulnerable to passwords R15. Explain the difference between "real" random number generators and pseudo" random number R16. Explain how a R17. Describe some biases that cause El. Calculate the search space for passwords in the following situa- a. Exactly seven characters long, chosen from uppercase and lowercase letters and digits. b. Seven characters or shorter, chosen from the printable ASCII ve basic attacks on character set. systems. 6.8.2 Exercises pe of authentication xamined in this tions: d. 14 characters or shorter, mixed case letters only. E2. Some password systems set a minimum length for passwords. We want to compare two systems ferences between the hreats described in in which the maximum password length is 16 characters, and passwords may contain any printable ASCII characters. One c. Exactly 14 characters long, mixed-case letters only. system allows passwords to be a length, while the other requires password hashing
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


