Question: End-to-end authentication and encryption are desired between two hosts. Draw figures similar to Figure 8.8 in the PLE (Figure 9.8 in the textbook) that show
End-to-end authentication and encryption are desired between two hosts. Draw figures similar to Figure 8.8 in the PLE (Figure 9.8 in the textbook) that show each of the following.
1)Transport adjacency with encryption applied before authentication.
2)A transport SA bundled inside a tunnel SA with encryption applied before authentication.
3)A transport SA bundled inside a tunnel SA with authentication applied before encryption.
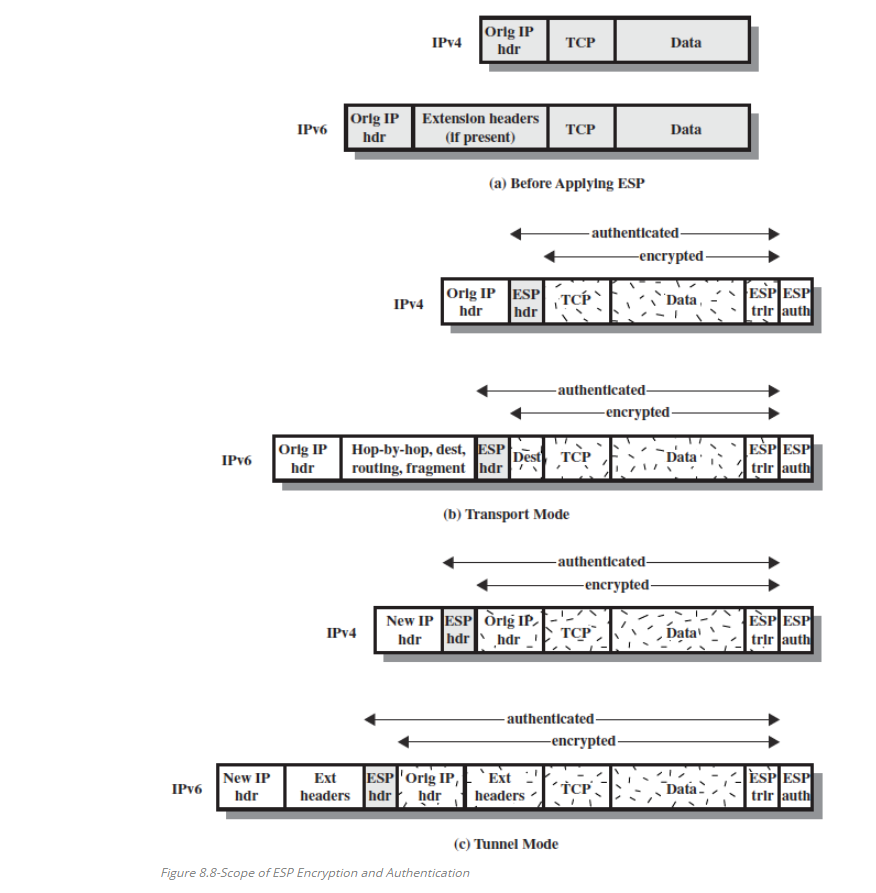
Orlg IP hdr IPv4 Data Orlg IPExtenslon headers IPv6 hdr (If present) Data (a) Before Applying ESP authenticated encrypted ESPES trir aut IPV4 hdr hdr -authenticated encrypted- Orlg IPHop-by-hop, dest, ESP routing, fragment hdr Data* ' ESPESI /1 trir laut IPv6 hdr (b) Transport Mode -authenticated encrypted New IP ESP Orig IP- ESP ES IPv4 . TOP hdr hdrhdr authenticated encrypted Ext ESP Orig IP,Ext headers hdr hdrheaders New IP IPv6 hdr (C)Tunnel Mode Figure 8.8-Scope of ESP Encryption and Authentication
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


