Question: End-to-end authentication and encryption are desired between two hosts. Draw figures similar to Figure 19.8 that show each of the following. a. Transport adjacency with
End-to-end authentication and encryption are desired between two hosts. Draw figures similar to Figure 19.8 that show each of the following.
a. Transport adjacency with encryption applied before authentication.
b. A transport SA bundled inside a tunnel SA with encryption applied before authentication.
c. A transport SA bundled inside a tunnel SA with authentication applied before encryption.
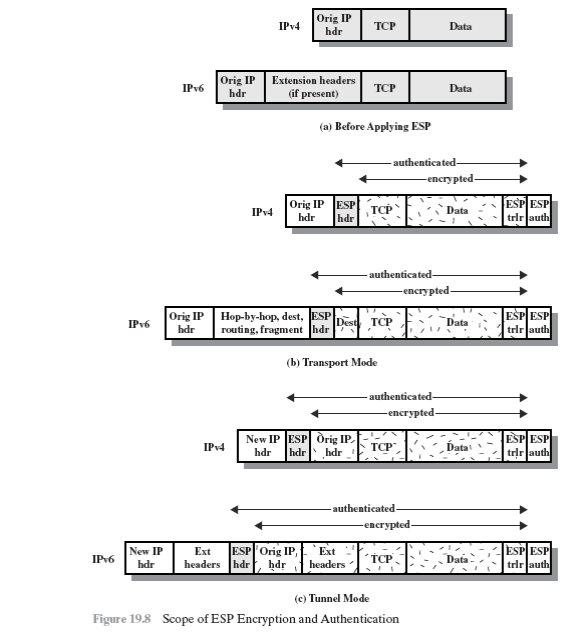
Orig IP hdr IPv4 TCP Data Orig IP hdr Extension headers if present) IPv6 TCP Data (a) Before Applying ESP Orig IP ESP ESPIESP trlr auth IPv4 TCP Data Orig IP hdr Hop-by-hop, dest ESP routing, fragmenthdr ESPIESP tdr auth Dest TCP Data (b) Transport Mode New IP ESP Orig IP hdr hdrhdr ESPESP trlr auth IPv4 authenticated New IP Ext ESP Orig IP, Ext headers [hdr hdr headers -..Data . ,' IP 6 TCP- trlr auth (c) Tunnel Mode Figure 19.8 Scope of ESP Encryption and Authentication
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


