Question: Explain why both authentication and access control are needed to implement OS security. (4 marks) List the basic steps that apply to most OS
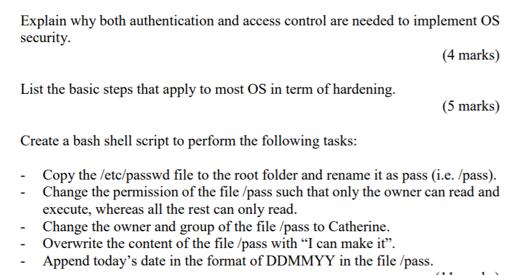
Explain why both authentication and access control are needed to implement OS security. (4 marks) List the basic steps that apply to most OS in term of hardening. (5 marks) Create a bash shell script to perform the following tasks: Copy the /etc/passwd file to the root folder and rename it as pass (i.e. /pass). Change the permission of the file /pass such that only the owner can read and execute, whereas all the rest can only read. Change the owner and group of the file/pass to Catherine. Overwrite the content of the file /pass with "I can make it". Append today's date in the format of DDMMYY in the file /pass.
Step by Step Solution
3.55 Rating (159 Votes )
There are 3 Steps involved in it
Authentication and Access Control for OS Security Authentication and access control are crucial components of OS security Authentication Definition Au... View full answer

Get step-by-step solutions from verified subject matter experts


