Question: Hello, please write with full explanation when answering the questions because I will be using it for understanding and revision purposes. This regards Computer Security.
Hello, please write with full explanation when answering the questions because I will be using it for understanding and revision purposes. This regards Computer Security. Thank you.
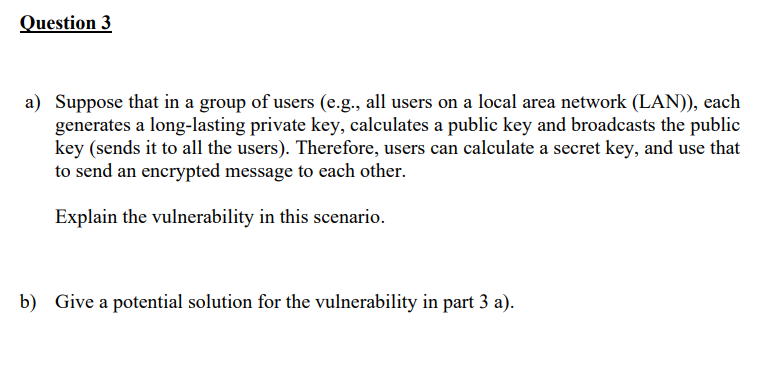
a) Suppose that in a group of users (e.g., all users on a local area network (LAN)), each generates a long-lasting private key, calculates a public key and broadcasts the public key (sends it to all the users). Therefore, users can calculate a secret key, and use that to send an encrypted message to each other. Explain the vulnerability in this scenario. b) Give a potential solution for the vulnerability in part 3 a)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


