Question: Hello, please write with full explanation when answering the questions because I will be using it for understanding and revision purposes. This regards Computer Security.
Hello, please write with full explanation when answering the questions because I will be using it for understanding and revision purposes. This regards Computer Security. Thank you.
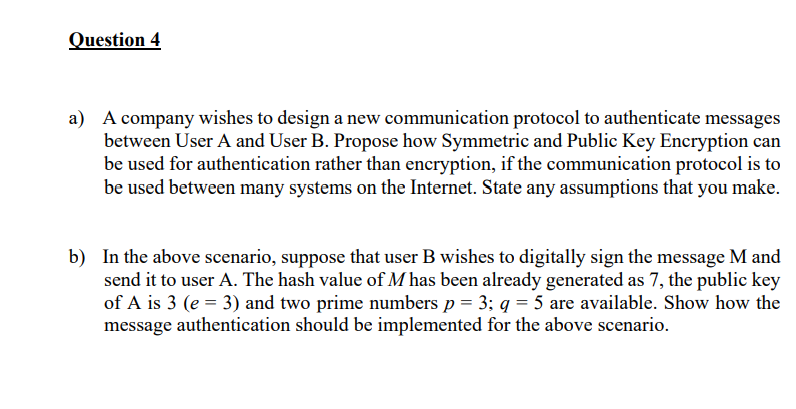
a) A company wishes to design a new communication protocol to authenticate messages between User A and User B. Propose how Symmetric and Public Key Encryption can be used for authentication rather than encryption, if the communication protocol is to be used between many systems on the Internet. State any assumptions that you make. b) In the above scenario, suppose that user B wishes to digitally sign the message M and send it to user A. The hash value of M has been already generated as 7 , the public key of A is 3(e=3) and two prime numbers p=3;q=5 are available. Show how the message authentication should be implemented for the above scenario
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


