Question: How is SSH different from Telnet? SSH makes connections over the network, whereas Telnet is for out-of-band access. SSH provides security to remote sessions
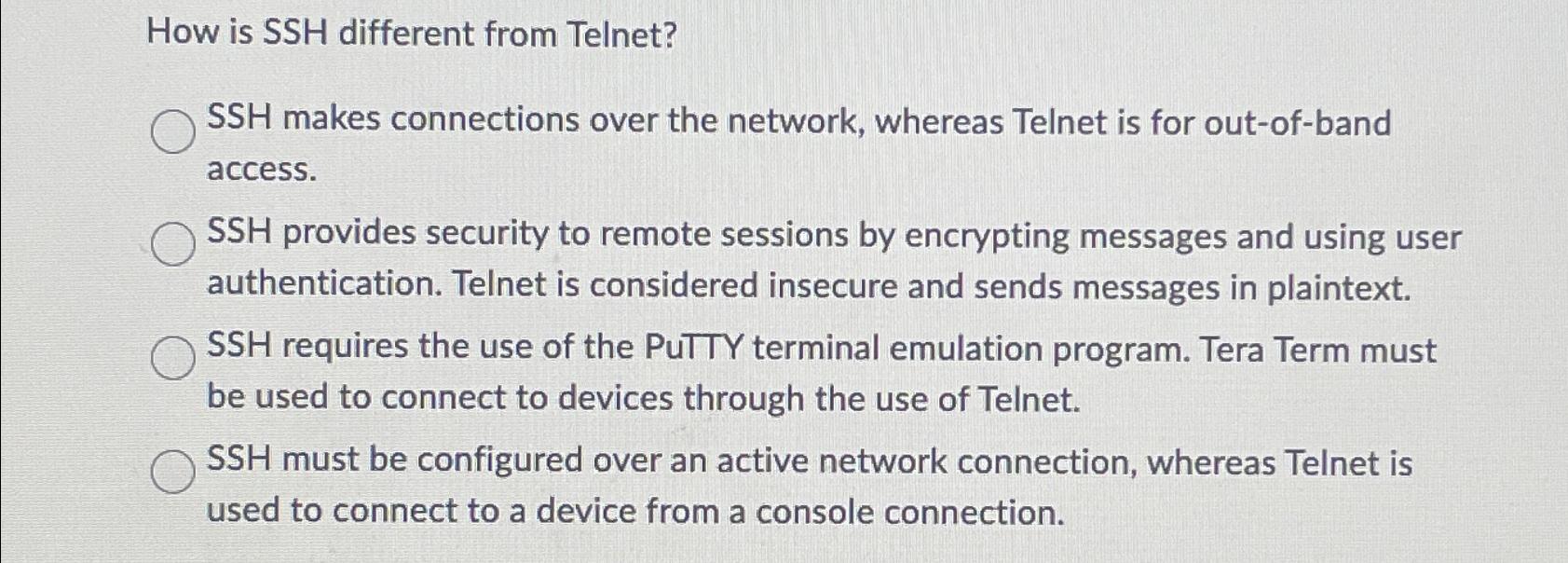
How is SSH different from Telnet? SSH makes connections over the network, whereas Telnet is for out-of-band access. SSH provides security to remote sessions by encrypting messages and using user authentication. Telnet is considered insecure and sends messages in plaintext. SSH requires the use of the PuTTY terminal emulation program. Tera Term must be used to connect to devices through the use of Telnet. SSH must be configured over an active network connection, whereas Telnet is used to connect to a device from a console connection.
Step by Step Solution
There are 3 Steps involved in it
The correct answer to the question How is SSH different from Telnet is SSH provides security to ... View full answer

Get step-by-step solutions from verified subject matter experts


