Question: Identify the network - based attack in which the attacker eavesdrops on existing network connections to intrude, read, and modify the data or insert fraudulent
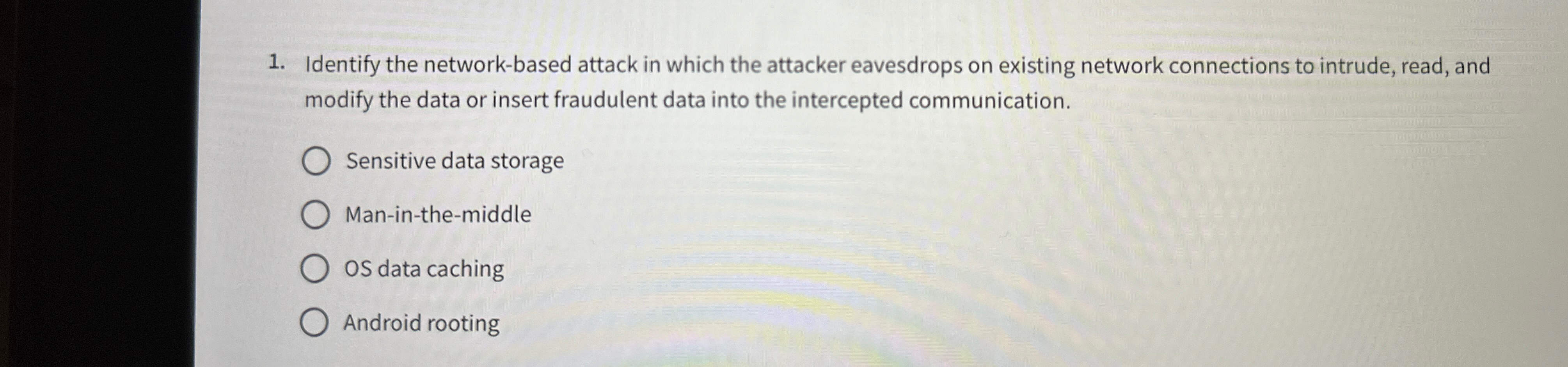
Identify the networkbased attack in which the attacker eavesdrops on existing network connections to intrude, read, and modify the data or insert fraudulent data into the intercepted communication.
Sensitive data storage
Maninthemiddle
OS data caching
Android rooting
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


