Instructions: You are presented with a list of some risks and threats associated with the domains...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
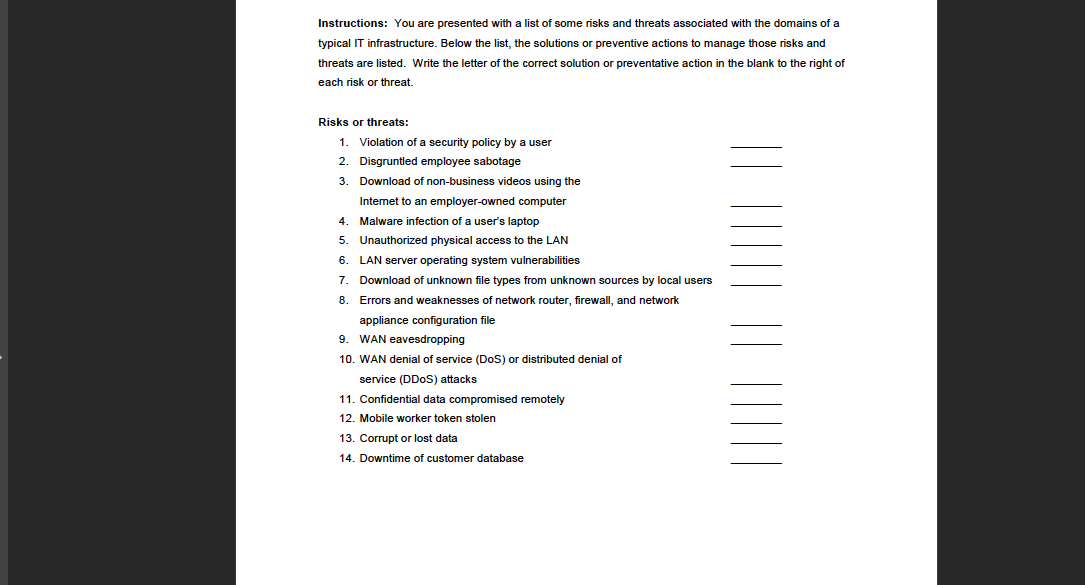
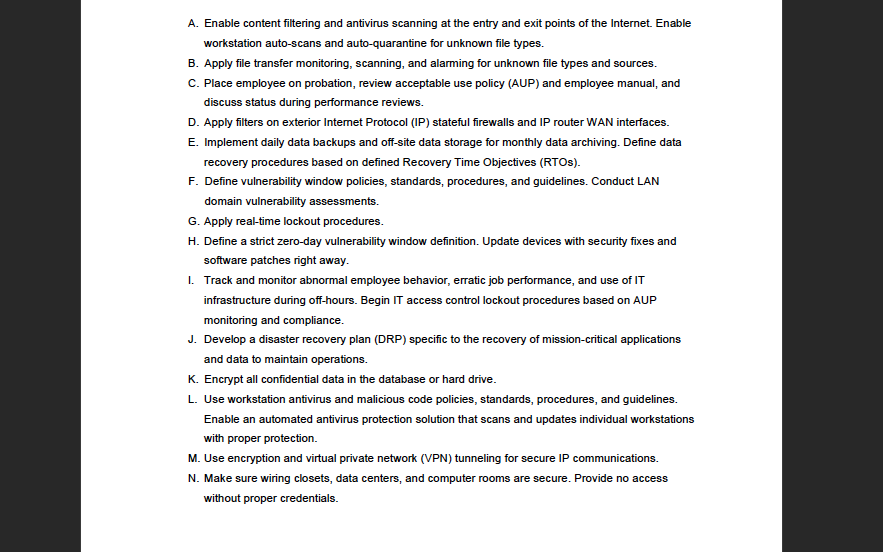
Instructions: You are presented with a list of some risks and threats associated with the domains of a typical IT infrastructure. Below the list, the solutions or preventive actions to manage those risks and threats are listed. Write the letter of the correct solution or preventative action in the blank to the right of each risk or threat. Risks or threats: 1. Violation of a security policy by a user 2. Disgruntled employee sabotage 3. Download of non-business videos using the Internet to an employer-owned computer 4. Malware infection of a user's laptop 5. Unauthorized physical access to the LAN 6. LAN server operating system vulnerabilities 7. Download of unknown file types from unknown sources by local users 8. Errors and weaknesses of network router, firewall, and network appliance configuration file 9. WAN eavesdropping 10. WAN denial of service (DoS) or distributed denial of service (DDoS) attacks 11. Confidential data compromised remotely 12. Mobile worker token stolen 13. Corrupt or lost data 14. Downtime of customer database A. Enable content filtering and antivirus scanning at the entry and exit points of the Internet. Enable workstation auto-scans and auto-quarantine for unknown file types. B. Apply file transfer monitoring, scanning, and alarming for unknown file types and sources. C. Place employee on probation, review acceptable use policy (AUP) and employee manual, and discuss status during performance reviews. D. Apply filters on exterior Internet Protocol (IP) stateful firewalls and IP router WAN interfaces. E. Implement daily data backups and off-site data storage for monthly data archiving. Define data recovery procedures based on defined Recovery Time Objectives (RTOS). F. Define vulnerability window policies, standards, procedures, and guidelines. Conduct LAN domain vulnerability assessments. G. Apply real-time lockout procedures. H. Define a strict zero-day vulnerability window definition. Update devices with security fixes and software patches right away. I. Track and monitor abnormal employee behavior, erratic job performance, and use of IT infrastructure during off-hours. Begin IT access control lockout procedures based on AUP monitoring and compliance. J. Develop a disaster recovery plan (DRP) specific to the recovery of mission-critical applications and data to maintain operations. K. Encrypt all confidential data in the database or hard drive. L. Use workstation antivirus and malicious code policies, standards, procedures, and guidelines. Enable an automated antivirus protection solution that scans and updates individual workstations with proper protection. M. Use encryption and virtual private network (VPN) tunneling for secure IP communications. N. Make sure wiring closets, data centers, and computer rooms are secure. Provide no access without proper credentials. Instructions: You are presented with a list of some risks and threats associated with the domains of a typical IT infrastructure. Below the list, the solutions or preventive actions to manage those risks and threats are listed. Write the letter of the correct solution or preventative action in the blank to the right of each risk or threat. Risks or threats: 1. Violation of a security policy by a user 2. Disgruntled employee sabotage 3. Download of non-business videos using the Internet to an employer-owned computer 4. Malware infection of a user's laptop 5. Unauthorized physical access to the LAN 6. LAN server operating system vulnerabilities 7. Download of unknown file types from unknown sources by local users 8. Errors and weaknesses of network router, firewall, and network appliance configuration file 9. WAN eavesdropping 10. WAN denial of service (DoS) or distributed denial of service (DDoS) attacks 11. Confidential data compromised remotely 12. Mobile worker token stolen 13. Corrupt or lost data 14. Downtime of customer database A. Enable content filtering and antivirus scanning at the entry and exit points of the Internet. Enable workstation auto-scans and auto-quarantine for unknown file types. B. Apply file transfer monitoring, scanning, and alarming for unknown file types and sources. C. Place employee on probation, review acceptable use policy (AUP) and employee manual, and discuss status during performance reviews. D. Apply filters on exterior Internet Protocol (IP) stateful firewalls and IP router WAN interfaces. E. Implement daily data backups and off-site data storage for monthly data archiving. Define data recovery procedures based on defined Recovery Time Objectives (RTOS). F. Define vulnerability window policies, standards, procedures, and guidelines. Conduct LAN domain vulnerability assessments. G. Apply real-time lockout procedures. H. Define a strict zero-day vulnerability window definition. Update devices with security fixes and software patches right away. I. Track and monitor abnormal employee behavior, erratic job performance, and use of IT infrastructure during off-hours. Begin IT access control lockout procedures based on AUP monitoring and compliance. J. Develop a disaster recovery plan (DRP) specific to the recovery of mission-critical applications and data to maintain operations. K. Encrypt all confidential data in the database or hard drive. L. Use workstation antivirus and malicious code policies, standards, procedures, and guidelines. Enable an automated antivirus protection solution that scans and updates individual workstations with proper protection. M. Use encryption and virtual private network (VPN) tunneling for secure IP communications. N. Make sure wiring closets, data centers, and computer rooms are secure. Provide no access without proper credentials.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
You make a one-time investment of $400 and leave it for 5 years, earning an annual interest rate of 7%. How much interest will you have earned after 5 years? If you leave the entire amount in your...
-
Find a recent article from a computing magazine or academic journal on the topic of Operating Systems. It should be more of a "current events" type article...look for articles on some recent...
-
(LO2) Mark is a successful attorney specializing in mergers and acquisitions. He hires his 16-year-old son, Eric, to perform general office work and pays Eric \(\( \$ \) 100,000\). Will this income...
-
Journal entries for both buyer and seller periodic inventory system Non- GST version (a) Prepare general journal entries to record the following transactions (i) for Esther Ltd and (ii) for Barton...
-
Pueblo Service is a fast-growing chain of oil-change stores. The following data are available for last years services: Pueblo Service performed 396,000 oil changes last year. It had budgeted 360,000...
-
A multinational corporation is accused of environmental pollution and human rights violations in a foreign country where it operates. What legal challenges arise in holding the corporation...
-
During the current year, Ron and Anne sold the following assets: (Use the dividends and capital gains tax rates and tax rate schedules.) Capital Asset Market Value Tax Basis Holding Period L stock $...
-
hich of the following statements regarding the allocation of capital is true? Businesses seeking capital are not required to provide information to potential suppliers. Investors and financiers...
-
Explain the Model of the Motivation Process (Figure 4.2) with a real-life example. Personality Perception Learning Attitudes Unfulfilled Needs, Wants, and Desires Goal or Need Tension Drive Behavior...
-
/ Information needed to write the exam Tax calculation ( PIT ) Income up to PLN 1 2 0 , 0 0 0 - 1 2 % minus the tax - free amount Income above PLN 1 2 0 , 0 0 0 1 0 , 8 0 0 PLN 7 6 gr plus 3 2 %...
-
How many securities can be created when an eighteen-year Treasury bond is stripped into separately traded securities?
-
1. Choose just one of the following productivity management components and provide an example of your own work experience/ own research, on how this management element contributed or contributes to...
-
When providing advice to switch financial products under via an SOA - do you have to provide the financial impact in a dollar amount? is it enough to provide a recommendation to change product - give...
-
Explain which operations the following Matlab codes perform. X = 2: X = Y^Z: Z= X*Y X = Y\Z: X = Y/Z: A = [123 4]: size (A): length (A): A': zeros (3,4): B = [12 ;4 5 ;7 8 ): plot (x,y): stem (x,y,...
-
Reichenbach Co., organized in 2018, has set up a single account for all intangible assets. The following summary discloses the debit entries that have been recorded during 2018 and 2019. Instructions...
-
Discuss the main factors which are likely to affect resistance to, and the successful implementation of, management control systems.
-
To what extent do you feel there is a danger of organisations placing too much emphasis on financial and quantitative systems of control?
-
Relate critically the concepts and ideas of Tomorrows Company and the EFQM Excellence Model to practices in your own organisation.
-
Use the numbers for the alcohol and tobacco category from the table in the Application "Goods with a Large Consumer Surplus Loss from Price Increases" to draw a figure that illustrates the roles that...
-
Change the answer given in the Challenge Solution for the short run rather than for the long run.
-
Because many consumers choose between coffee and tea, the coffee and tea demand functions depend on both prices. Suppose the demand curves for coffee and tea are where \(Q_{c}\) is the quantity of...

Study smarter with the SolutionInn App