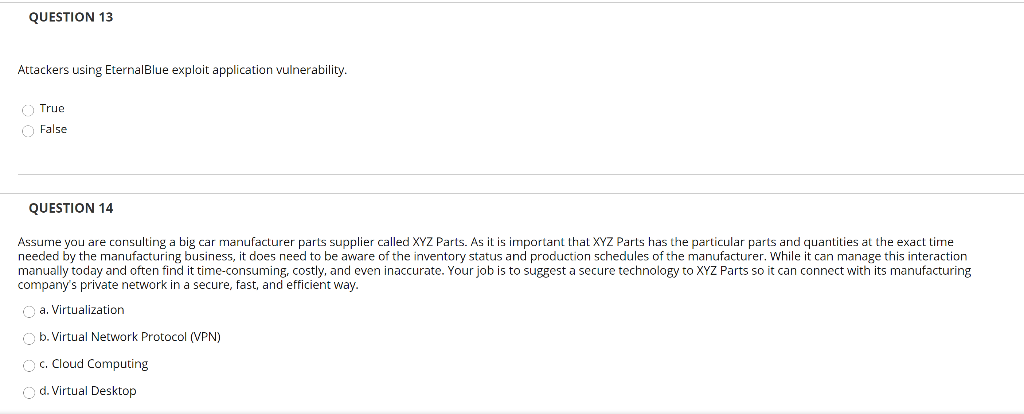
Question: need all asap please QUESTION 13 Attackers using EternalBlue exploit application vulnerability. (True False QUESTION 14 Assume you are consulting a big car manufacturer parts
 need all asap please
need all asap please
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


