Question: please i want full clear solution DONOT COPY 15 points) User Authentication. (7 points) Consider the following proposed authentication protocol between Alice and Bob based
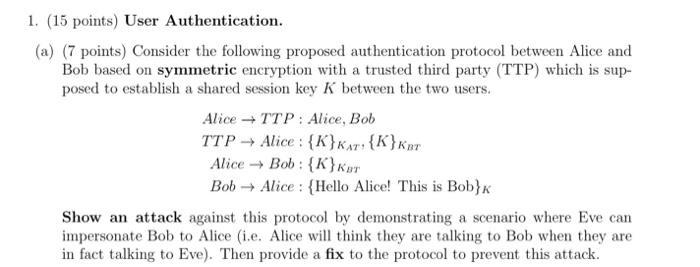
15 points) User Authentication. (7 points) Consider the following proposed authentication protocol between Alice and Bob based on symmetric encryption with a trusted third party (TTP) which is supposed to establish a shared session key K between the two users. AliceTTP:Alice,BobTTPAlice:{K}KAT,{K}KBTAliceBob:{K}KBTBobAlice:{HelloAlice!ThisisBob}K Show an attack against this protocol by demonstrating a scenario where Eve can impersonate Bob to Alice (i.e. Alice will think they are talking to Bob when they are in fact talking to Eve). Then provide a fix to the protocol to prevent this attack
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


