Prime numbers are of the outmost importance in pure mathematics, but they are also essential in...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
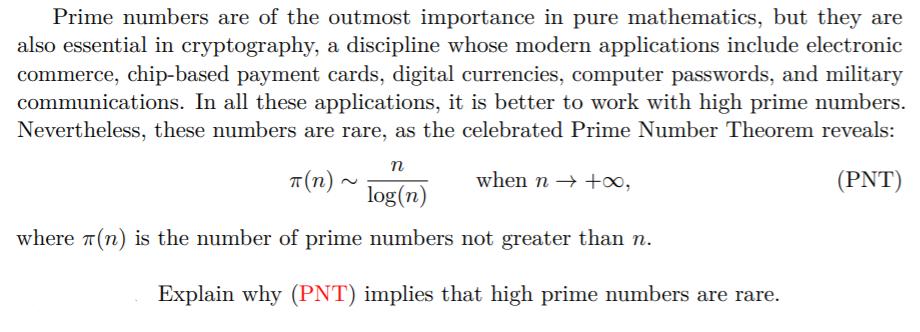
Prime numbers are of the outmost importance in pure mathematics, but they are also essential in cryptography, a discipline whose modern applications include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. In all these applications, it is better to work with high prime numbers. Nevertheless, these numbers are rare, as the celebrated Prime Number Theorem reveals: T(n) when n +, (PNT) n log(n) where 7(n) is the number of prime numbers not greater than n. Explain why (PNT) implies that high prime numbers are rare. Prime numbers are of the outmost importance in pure mathematics, but they are also essential in cryptography, a discipline whose modern applications include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. In all these applications, it is better to work with high prime numbers. Nevertheless, these numbers are rare, as the celebrated Prime Number Theorem reveals: T(n) when n +, (PNT) n log(n) where 7(n) is the number of prime numbers not greater than n. Explain why (PNT) implies that high prime numbers are rare.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
answer the question clearly You are building a flight-control system for which a convincing safety case must be made. Would you assign the tasks of safety requirements engineering, test case...
-
In Exercises 1126, determine whether each equation defines y as a function of x. x + y = 25
-
In each of Exercises 6.121-6.126, we have provided a normal probability plot of data from a sample of a population. In each case, assess the normality of the variable under consideration. a. b. c. -2...
-
Find the vertex of the graph. f ( x ) = 2 x ^ 2 3 x + 5
-
A 15-mph wind flows over a Quonset hut having a radius of \(12 \mathrm{ft}\) and a length of \(60 \mathrm{ft}\), as shown in Fig. P6.57. The upstream pressure and temperature are equal to those...
-
During the 2004 DHB audit, the companys independent auditors had considerable difficulty obtaining reliable audit evidence regarding the $7 million of obsolete vest components that allegedly had been...
-
A negative point-like charge of -45 nC is placed 2.0 cm away from an infinite planar sheet of positive charge. The surface charge density of the sheet is constant and has the value of + 0.20 nC/cm2 ....
-
The recommendations of respected wine critics such as Robert M. Parker, Jr. have a substantial effect on the price of wine. Vintages that earn higher ratings command higher prices and spark surges in...
-
Oz Credit Bank (OCB) is currently processing an application for a 3-year interest-only loan in the amount of $7.5 million from a customer in the seafood exporting business (Manta Pty Ltd). In its...
-
Which best describes a top-down migration? (Choose two.) A. The first step is to move all the modules to the module path. B. The first step is to move a single module to the module path. C. Most...
-
What command is the simplest way to list what modules a JAR depends on including package names? A. jdeps cookie.jar B. jdeps s cookie.jar C. jdeps jdkinternals cookie.jar D. jdeps --jdkinternals...
-
What command is the simplest way to list what modules a JAR depends on without listing package names? A. jdeps cookie.jar B. jdeps s cookie.jar C. jdeps jdkinternals cookie.jar D. jdeps...
-
Fill in the blanks to list a way of getting a lot of information useful in debugging modules: _______ -m x p y --______________. A. jar and show-modules B. jar and show-module-detail C. jar and...
-
What command could you run to print output like the following? A. java --all-modules B. java --describe-modules C. java --list-modules D. java --output-modules E. java --show-modules F. None of the...
-
To protect soil from erosion, some farmers plant winter cover crops such as winter wheat and rye. In addition to conserving soil, cover crops often increase crop yields in the row crops that follow...
-
Cable Corporation is 60% owned by Anna and 40% owned by Jim, who are unrelated. It has noncash assets, which it sells to an unrelated purchaser for $100,000 in cash and $900,000 in installment...
-
Repeat Exercise 3 using instead the Padé approximation of degree 5 with n = 3 and m = 2. Compare the results at each xi with those computed in Exercise 3.
-
Let A be a 3 3 matrix. Show that if A is the matrix obtained from A using any of the operations (E 1 ) (E 2 ), (E 1 ) (E 3 ), or (E 2 ) (E 3 ), then det A = det A.
-
Repeat Exercise 10 using Gaussian elimination with complete pivoting and three-digit rounding arithmetic. In Exercise 10 a. 58.9x 1 + 0.03x 2 = 59.2, 6.10x 1 + 5.31x 2 = 47.0. Actual solution [1, 10]...
-
A slider bearing consists of a sleeve surrounding a cylindrical shaft that is free to move axially within the sleeve. A lubricant (e.g., grease) is in the gap between the shaft and the sleeve to...
-
By making use of the analogies between the various transport models for molecular transport of conserved quantities, describe how you would set up an experiment to solve each of the following...
-
What is the "system" in Example 1.3? Example 1.3 With respect to Figure 1.1, consider the two parallel flat surfaces spaced 1 mm apart, with a Newtonian grease between them that has a viscosity of...

Study smarter with the SolutionInn App