Question: Question 23 2 pts Access violations can be discovered by examining the logs of a given system. O True O False D Question 24 2
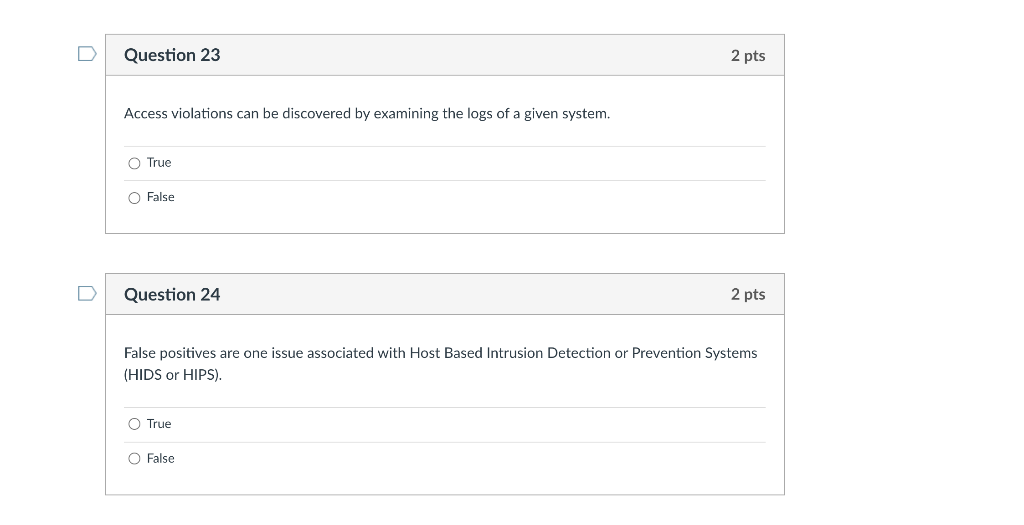
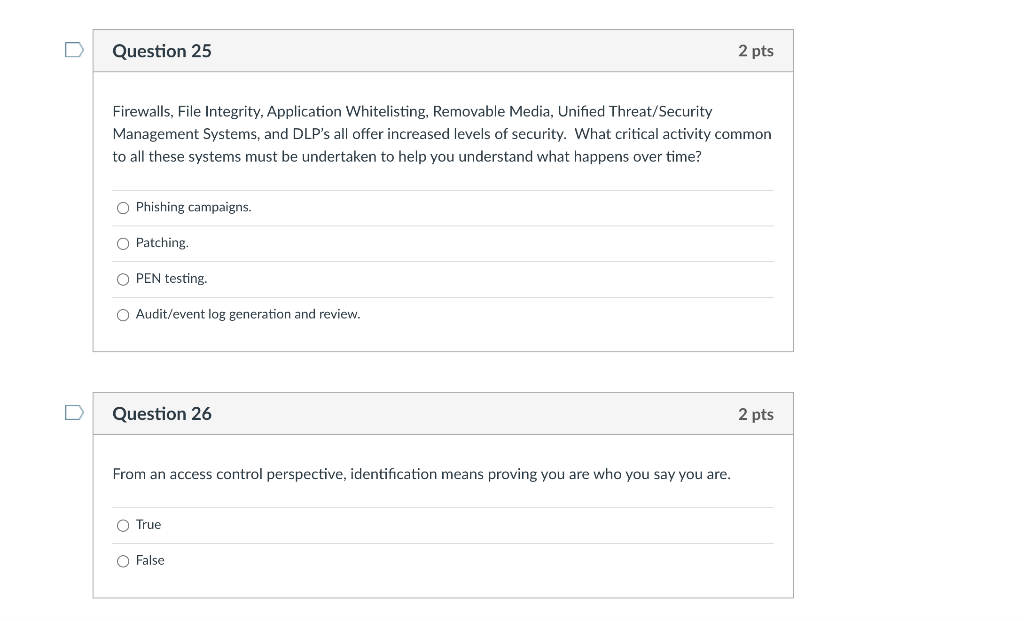
Question 23 2 pts Access violations can be discovered by examining the logs of a given system. O True O False D Question 24 2 pts False positives are one issue associated with Host Based Intrusion Detection or Prevention Systems (HIDS or HIPS). O True O False Question 25 2 pts Firewalls, File Integrity, Application Whitelisting, Removable Media, Unified Threat/Security Management Systems, and DLP's all offer increased levels of security. What critical activity common to all these systems must be undertaken to help you understand what happens over time? O Phishing campaigns. Patching OPEN testing. O Audit/event log generation and review. u Question 26 2 pts From an access control perspective, identification means proving you are who you say you are. True O False
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


