Question: Question 3 (Brief answer): Suppose Bob has the following protocol for authenticating Alice I'm Alice Challenge R Encrypt(R)K Alice Bob 0 The first two messages
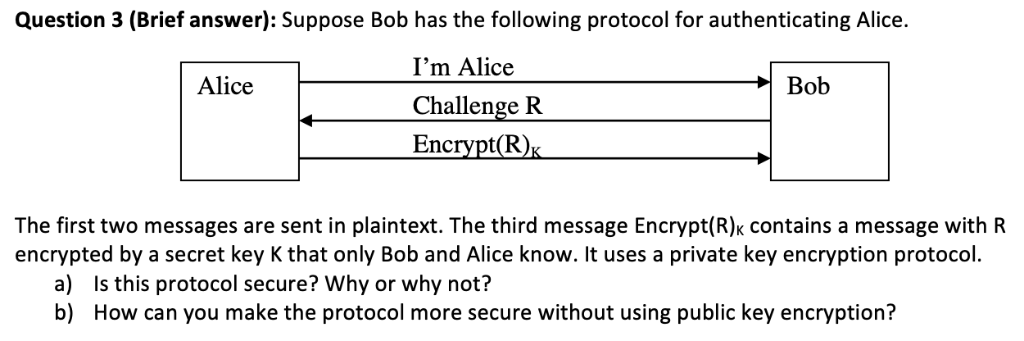
Question 3 (Brief answer): Suppose Bob has the following protocol for authenticating Alice I'm Alice Challenge R Encrypt(R)K Alice Bob 0 The first two messages are sent in plaintext. The third message Encrypt(R): contains a message with R encrypted by a secret key K that only Bob and Alice know. It uses a private key encryption protocol a) Is this protocol secure? Why or why not? How can you make the protocol more secure without using public key encryption? b)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


