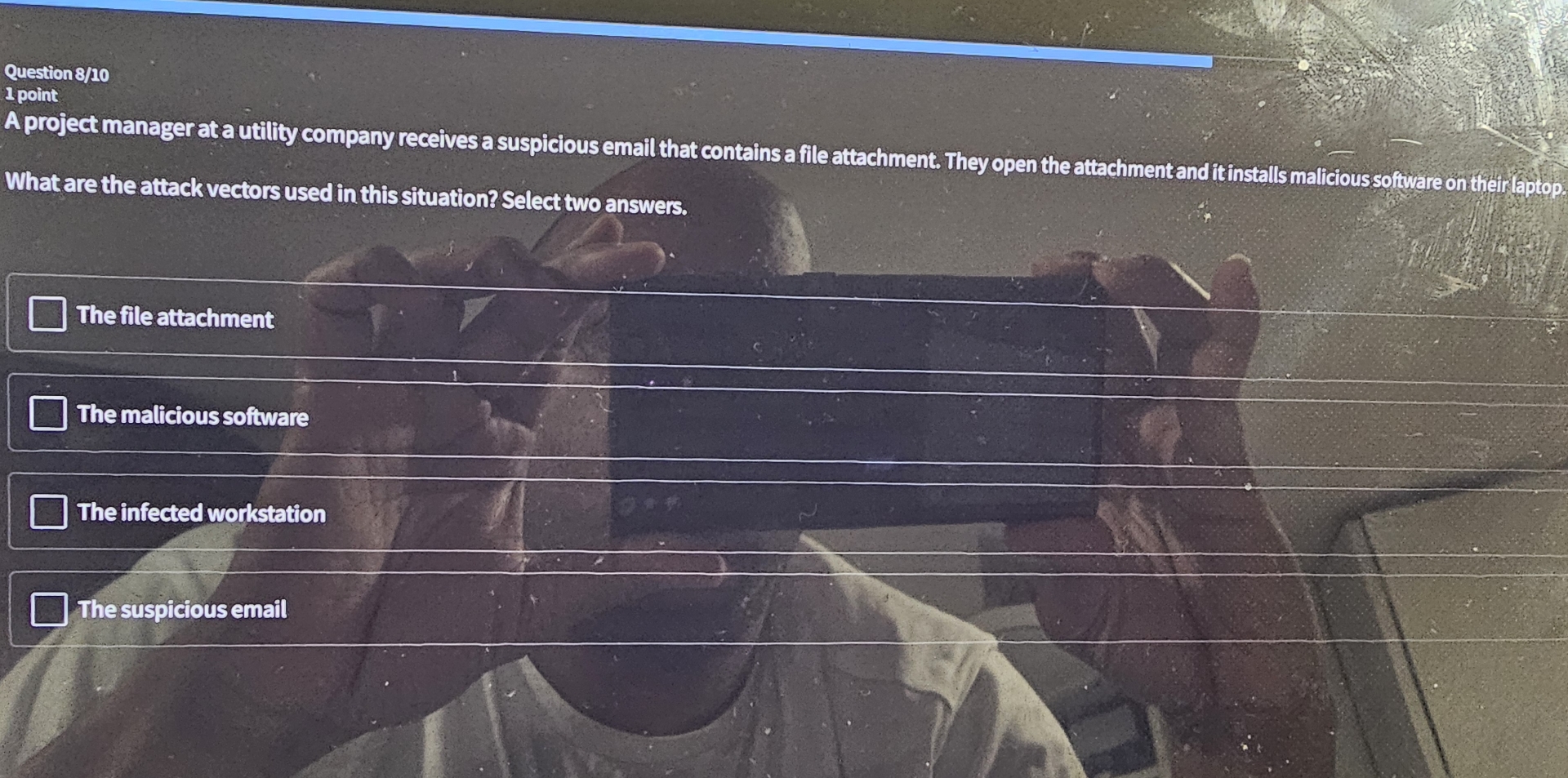
Question: Question 8 1 0 1 point What are the attack vectors used in this situation? Select two answers. The fileattachment The malicious software The infected
Question
point
What are the attack vectors used in this situation? Select two answers.
The fileattachment
The malicious software
The infected workstation
The suspicious email
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


