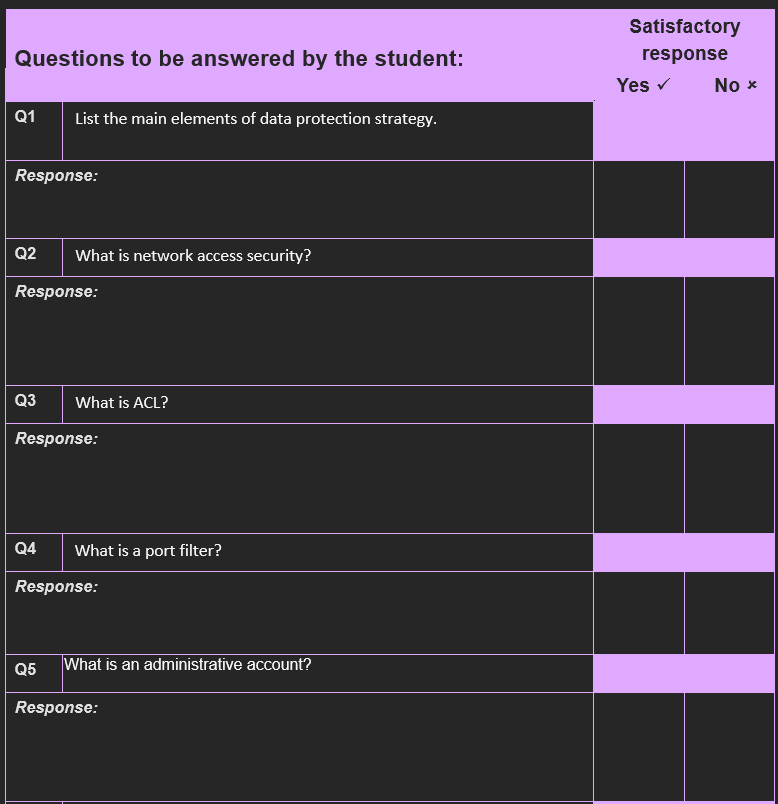
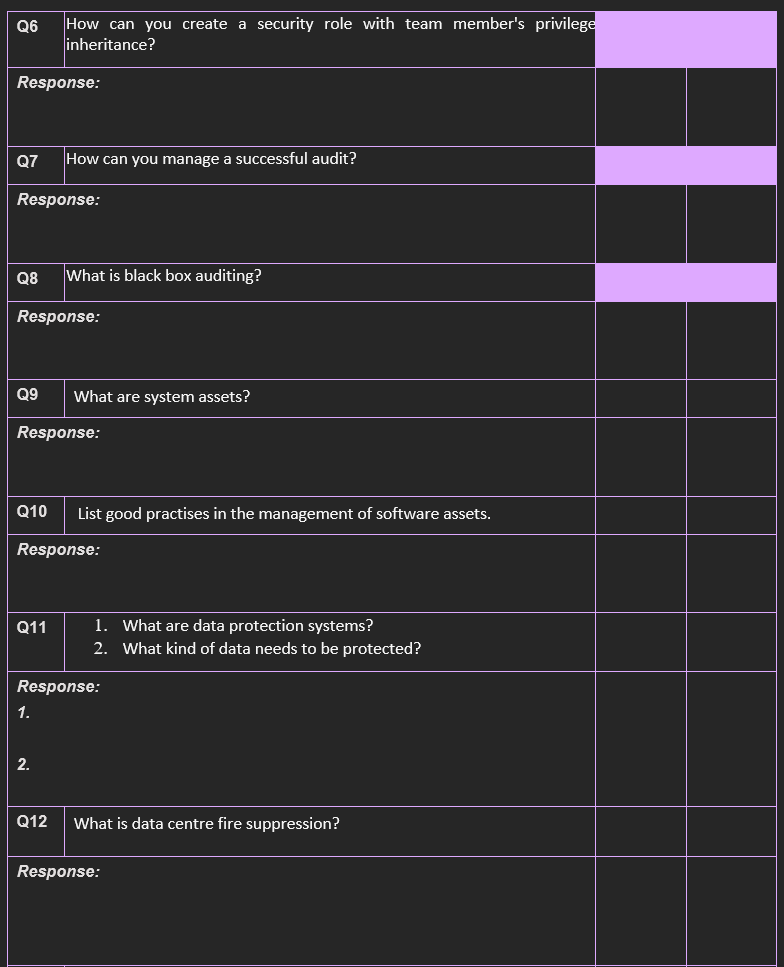
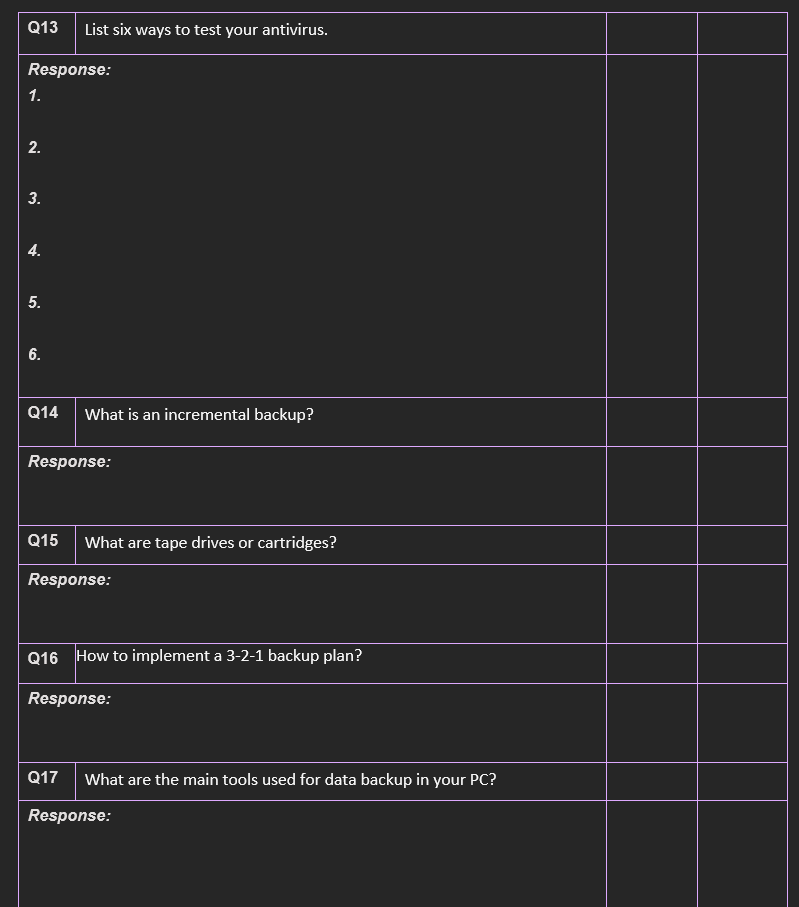
Questions to be answered by the student: Q1 Response: Q2 Q3 List the main elements of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
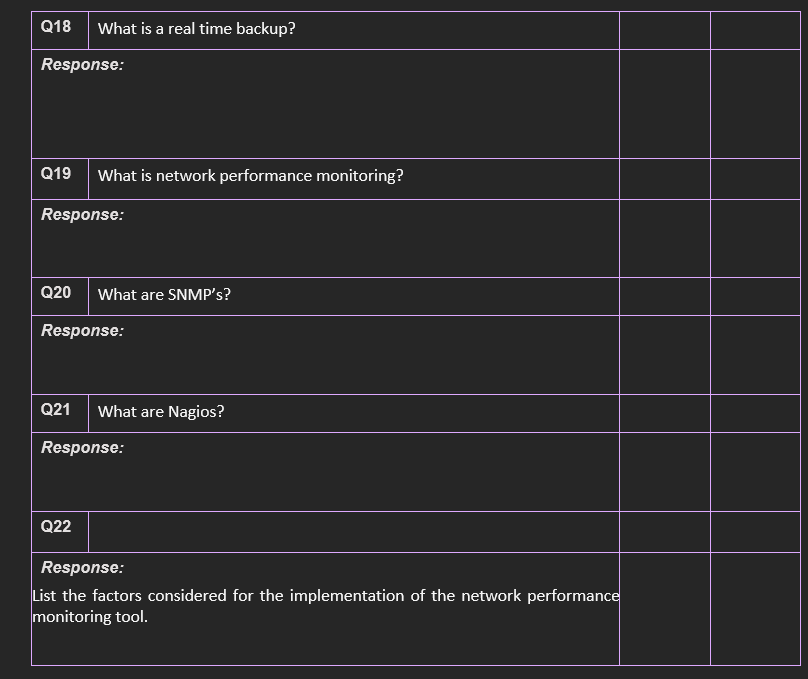
Questions to be answered by the student: Q1 Response: Q2 Q3 List the main elements of data protection strategy. Response: Q4 What is network access security? Response: Q5 What is ACL? What is a port filter? Response: What is an administrative account? Response: Satisfactory response Yes No x Q6 How can you create a security role with team member's privilege inheritance? Response: Q7 Response: Q8 Q9 Response: Q10 How can you manage a successful audit? Response: Q11 What is black box auditing? 1. Response: 2. What are system assets? Q12 List good practises in the management of software assets. Response: 1. What are data protection systems? 2. What kind of data needs to be protected? What is data centre fire suppression? Response: Q13 List six ways to test your antivirus. Response: 1. 2. 3. 4. 5. 6. Q14 What is an incremental backup? Response: Q15 What are tape drives or cartridges? Response: Q16 How to implement a 3-2-1 backup plan? Response: Q17 What are the main tools used for data backup in your PC? Response: Q18 What is a real time backup? Response: Q19 What is network performance monitoring? Response: Q20 What are SNMP's? Response: Q21 What are Nagios? Response: Q22 Response: List the factors considered for the implementation of the network performance monitoring tool. Questions to be answered by the student: Q1 Response: Q2 Q3 List the main elements of data protection strategy. Response: Q4 What is network access security? Response: Q5 What is ACL? What is a port filter? Response: What is an administrative account? Response: Satisfactory response Yes No x Q6 How can you create a security role with team member's privilege inheritance? Response: Q7 Response: Q8 Q9 Response: Q10 How can you manage a successful audit? Response: Q11 What is black box auditing? 1. Response: 2. What are system assets? Q12 List good practises in the management of software assets. Response: 1. What are data protection systems? 2. What kind of data needs to be protected? What is data centre fire suppression? Response: Q13 List six ways to test your antivirus. Response: 1. 2. 3. 4. 5. 6. Q14 What is an incremental backup? Response: Q15 What are tape drives or cartridges? Response: Q16 How to implement a 3-2-1 backup plan? Response: Q17 What are the main tools used for data backup in your PC? Response: Q18 What is a real time backup? Response: Q19 What is network performance monitoring? Response: Q20 What are SNMP's? Response: Q21 What are Nagios? Response: Q22 Response: List the factors considered for the implementation of the network performance monitoring tool.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The three way TCP handshake between sender and receiver A)requires a SYN packet from the sender to be answered by a SYN, ACKpacket from the recipeint which is followed by an ACK packet fromthe sender...
-
? Fisheries Bhd is a small listed company involves in fishing and selling fish to the public via retail outlets. The company owns a building that was acquired in early September 2014 for RM1,200,000,...
-
An office building owned by Milo was destroyed by Hurricane Mel on September 25, 2015. On October 2, 2015, the President of the United States declared the area where the office building was located a...
-
When two waves interfere, can the amplitude of the resultant wave be greater than either of the two original waves? Under what conditions?
-
A friend has asked you for help. She is an entrepreneur and would like to start a company to pursue her dream of designing and selling a line of childrens toys. She has heard the term stakeholder...
-
Cherry Cotta makes custom ordered clay pots for residential gardens. Below is cost information regarding its latest job. a. Materials were purchased on account. $18,996 purchased b. A materials...
-
You can find this question from Excel worksheet "poison pill question". Twilight has 1,000,000 shares outstanding, and the current stock price is $25 per share. Yesterday, Activist Apollo made a...
-
Spartan Corp. is a firm with no cash on hand but lots of great ideas. The firm currently has 100,000 shares outstanding. All of these shares are held by the firm's founders, executives, and...
-
Compare and contrast a single-country marketing strategy with a global marketing strategy (GMS).
-
Define competitive advantage and identify the key conceptual frameworks that guide decision makers in the strategic planning process.
-
Explain the categories of economic development used by the World Bank, and identify the key emerging country markets at each stage of development.
-
Define hypercompetitive industry and list the key arenas in which dynamic strategic interactions take place.
-
Why does it seem that the growth of global business and global marketing is almost inevitably associated with ethical issues and corporate social responsibility?
-
FIFO, LIFO and weighted average Computadoras del Futuro made several purchases and sales in April. He had operating expenses of $ 1,800. Prepare three income statements: one using the FIFO method,...
-
Identify the most stable compound:
-
Adriana Lopez expected sales of her line of computer workstation furniture to equal 300 workstations (at a sales price of $3,000) for 2010. The workstations manufacturing costs include the following....
-
How is a scatter diagram used to identify and measure the behavior of a companys costs?
-
Lenitnes Company is considering an investment in technology to improve its operations. The investment will require an initial outlay of $250,000 and will yield the following expected cash flows....
-
An economist believes that the median income of lawyers who recently graduated from law school is more than \(\$ 64,000\). He queries a random sample of 12 lawyers and obtains the accompanying data....
-
The median is different from 120. An analysis of the data reveals that there are 35 minus signs and 28 plus signs. Use the sign test to test the given alternative hypothesis at the \(\alpha=0.05\)...
-
One important variable to consider in trading stock is the daily volume. Volume is measured in number of shares traded in the stock. Stocks with lower volume tend to have more variability in the...

Study smarter with the SolutionInn App