Suppose Abu goes to the coffee shop nearby with free WiFi facility. He finishes his works...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
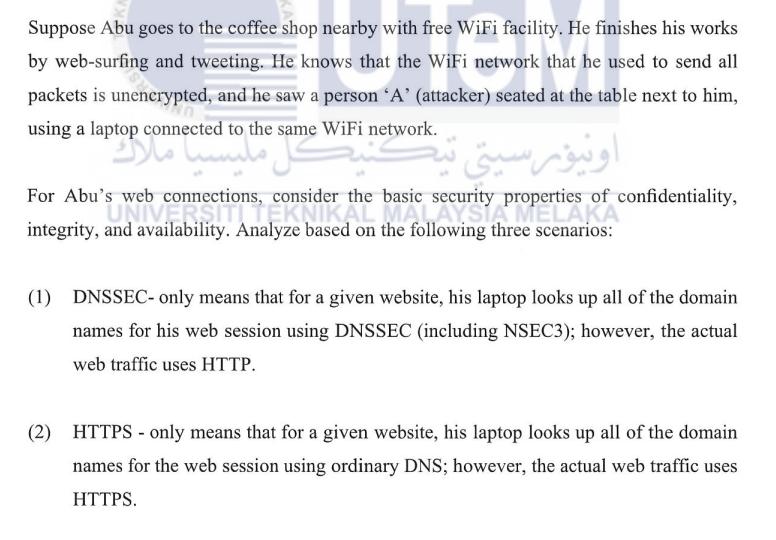
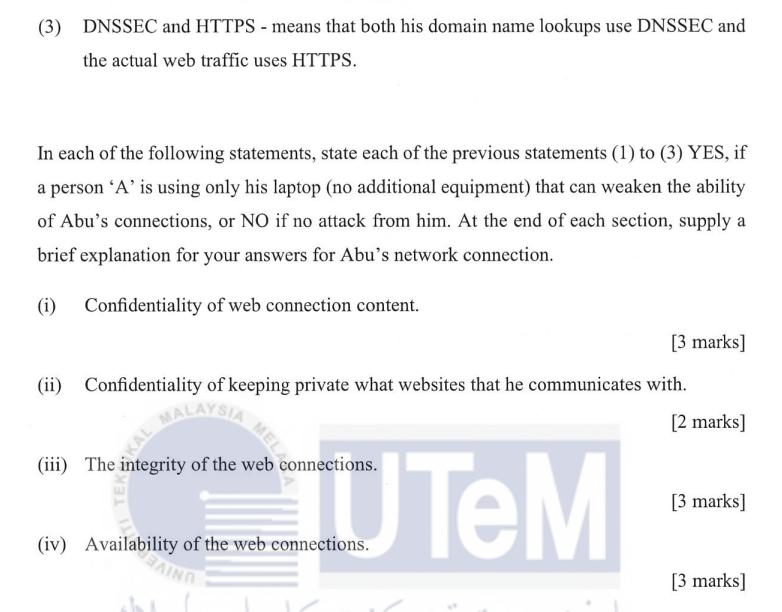
Suppose Abu goes to the coffee shop nearby with free WiFi facility. He finishes his works by web-surfing and tweeting. He knows that the WiFi network that he used to send all packets is unencrypted, and he saw a person 'A' (attacker) seated at the table next to him, using a laptop connected to the same WiFi network. Esto taml ونیورسیتی For Abu's web connections, consider the basic se integrity, and availability. Analyze based on the following three scenarios: basic security P of confidentiality, properties of c (1) DNSSEC- only means that for a given website, his laptop looks up all of the domain names for his web session using DNSSEC (including NSEC3); however, the actual web traffic uses HTTP. (2) HTTPS - only means that for a given website, his laptop looks up all of the domain names for the web session using ordinary DNS; however, the actual web traffic uses HTTPS. (3) DNSSEC and HTTPS - means that both his domain name lookups use DNSSEC and the actual web traffic uses HTTPS. In each of the following statements, state each of the previous statements (1) to (3) YES, if a person 'A' is using only his laptop (no additional equipment) that can weaken the ability. of Abu's connections, or NO if no attack from him. At the end of each section, supply a brief explanation for your answers for Abu's network connection. (1) Confidentiality of web connection content. [3 marks] (ii) Confidentiality of keeping private what websites that he communicates with. MALAYSIA [2 marks] KALA KEK MELA (iii) The integrity of the web connections. (iv) Availability of the web connections. TeM [3 marks] [3 marks] Suppose Abu goes to the coffee shop nearby with free WiFi facility. He finishes his works by web-surfing and tweeting. He knows that the WiFi network that he used to send all packets is unencrypted, and he saw a person 'A' (attacker) seated at the table next to him, using a laptop connected to the same WiFi network. Esto taml ونیورسیتی For Abu's web connections, consider the basic se integrity, and availability. Analyze based on the following three scenarios: basic security P of confidentiality, properties of c (1) DNSSEC- only means that for a given website, his laptop looks up all of the domain names for his web session using DNSSEC (including NSEC3); however, the actual web traffic uses HTTP. (2) HTTPS - only means that for a given website, his laptop looks up all of the domain names for the web session using ordinary DNS; however, the actual web traffic uses HTTPS. (3) DNSSEC and HTTPS - means that both his domain name lookups use DNSSEC and the actual web traffic uses HTTPS. In each of the following statements, state each of the previous statements (1) to (3) YES, if a person 'A' is using only his laptop (no additional equipment) that can weaken the ability. of Abu's connections, or NO if no attack from him. At the end of each section, supply a brief explanation for your answers for Abu's network connection. (1) Confidentiality of web connection content. [3 marks] (ii) Confidentiality of keeping private what websites that he communicates with. MALAYSIA [2 marks] KALA KEK MELA (iii) The integrity of the web connections. (iv) Availability of the web connections. TeM [3 marks] [3 marks]
Expert Answer:
Answer rating: 100% (QA)
Answer 1 DNSSEConly With DNSSEC the confidentiality of domain name lookups is increased because DNSSEC provides authenticity and integrity for the inf... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
How can your knowledge of meat and meat cookery be used to understand protein substitutions for vegan dishes, such as tofu, texturized soy protein, grains, or beans?
-
How would you define supply chain risk?
-
A manufacturer produces both a deluxe and a standard model of an automatic sander designed for home use. Selling prices obtained from a sample of retail outlets follow. a. The manufacturer's...
-
You shoot a beam of electrons through a double slit to make an interference pattern. After noting the properties of the pattern, you then double the speed of the electrons. What effect would this...
-
Clark Paints: The production department has been investigating possible ways to trim total production costs. One possibility currently being examined is to make the paint cans instead of purchasing...
-
Think back to the case study DECIEM, which you read earlier this semester and discussed on meskanas. The case examined -among other things- the anti-Black Friday marketing communications campaign of...
-
Question 6 10 pts You have been hired to do a study of the cooking process at a restaurant. The manager has hired your consulting firm because he has heard that you specialize in work measurement...
-
Jesse art gallery sells pictures for 50 each Jesse pays 20 for the print and frame and pays the sales clerk 20% of the sale price as a commission. Jesse has 7000 of monthly fixed costs as well. How...
-
A, B, C, and D formed a general partnership. Their written partnership agreement provides that profits and losses are shared as follows: A 40%; B 30%; C 20%; and D 10%. Their capital account balances...
-
A gifts $100,000 to a trust for the benefit of A's grandchild. GC. GC has the right to withdraw up to $17,000 from the trust each year and A makes no other gifts to GC during the year. The trust has...
-
Financial indicators are impacted by the indicators of capacity, , and performance. The costs of resources used in providing nursing care the supplies required are known as what?
-
Barry is currently registered as a Maryland tax preparer. A longtime client has written him requesting a copy of their 2020 and 2021 returns because their copies were lost in a fire. What...
-
a) What is the correct mean particle diameter to be used in the Ergun equation? How can this diameter be derived from a volume distribution? [2]
-
Define the term utility software and give two examples.
-
Suppose two nodes, A and B, are attached to opposite ends of an 800 m cable, and that they each have one frame of I,SOO bits (including all headers and preambles) to send to each other. Both nodes...
-
Discuss how a hierarchical organization of the Internet has made it possible to scale to millions of users.
-
In protocol rdt3. 0, the ACK packets flowing from the receiver 10 the sender do not have sequence numbers (although they do have an ACK field that contains the sequence number of the packet they are...
-
Long Weekend Ltd suffered a severe drop in sales and profit performance for the year ended 30 June 2019. The income statement revealed that net sales were $1 500 000 with a profit of $310 000. Unit...
-
TMP Human Resource Consulting had the following contribution margin income statement for the year ended 2019. Required Answer each of the following independent situations. (a) Explain how an...
-
Explain how budgeting helps in running a business efficiently and effectively.

Study smarter with the SolutionInn App


