Question: Suppose we are using a three-message mutual authentication protocol, and Alice initiates contact with Bob. Suppose we wish Bob to be a stateless server, and
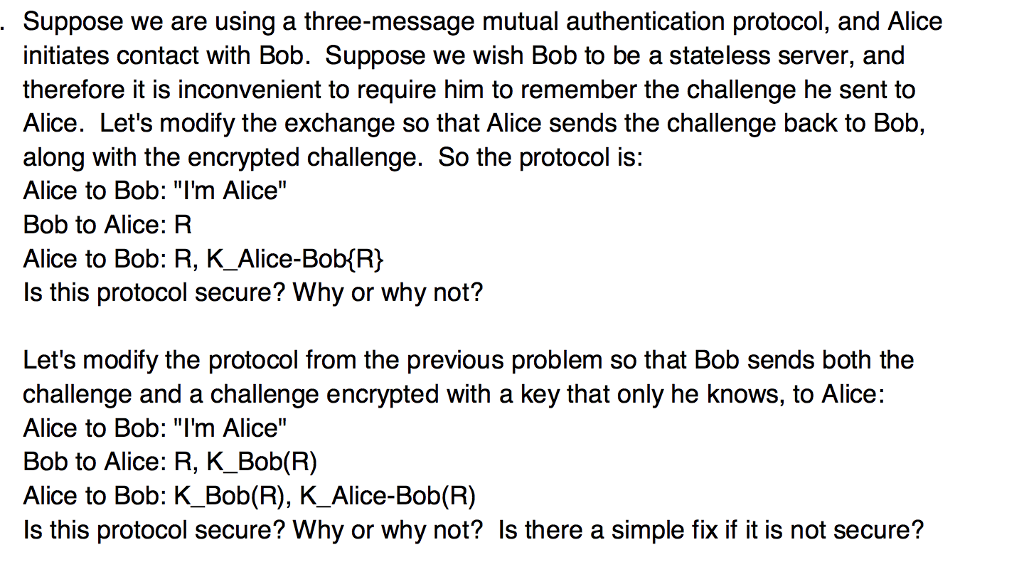
Suppose we are using a three-message mutual authentication protocol, and Alice initiates contact with Bob. Suppose we wish Bob to be a stateless server, and therefore it is inconvenient to require him to remember the challenge he sent to Alice. Let's modify the exchange so that Alice sends the challenge back to Bob, along with the encrypted challenge. So the protocol is: Alice to Bob: "I'm Alice" Bob to Alice: R Alice to Bob: R, K_Alice-Bob(R) Is this protocol secure? Why or why not? Let's modify the protocol from the previous problem so that Bob sends both the challenge and a challenge encrypted with a key that only he knows, to Alice Alice to Bob: "I'm Alice" Bob to Alice: R, K_Bob(R) Alice to Bob: K_Bob(R), K_Alice-Bob(R) Is this protocol secure? Why or why not? Is there a simple fix if it is not secure? Suppose we are using a three-message mutual authentication protocol, and Alice initiates contact with Bob. Suppose we wish Bob to be a stateless server, and therefore it is inconvenient to require him to remember the challenge he sent to Alice. Let's modify the exchange so that Alice sends the challenge back to Bob, along with the encrypted challenge. So the protocol is: Alice to Bob: "I'm Alice" Bob to Alice: R Alice to Bob: R, K_Alice-Bob(R) Is this protocol secure? Why or why not? Let's modify the protocol from the previous problem so that Bob sends both the challenge and a challenge encrypted with a key that only he knows, to Alice Alice to Bob: "I'm Alice" Bob to Alice: R, K_Bob(R) Alice to Bob: K_Bob(R), K_Alice-Bob(R) Is this protocol secure? Why or why not? Is there a simple fix if it is not secure
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


