Question: Task 2: Create a Risk Management Plan that corresponds to the research you have made in Task No. 1. Example of Risk Management Plan: Threat
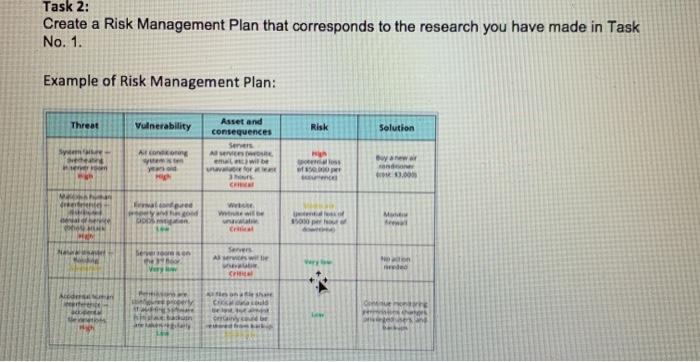
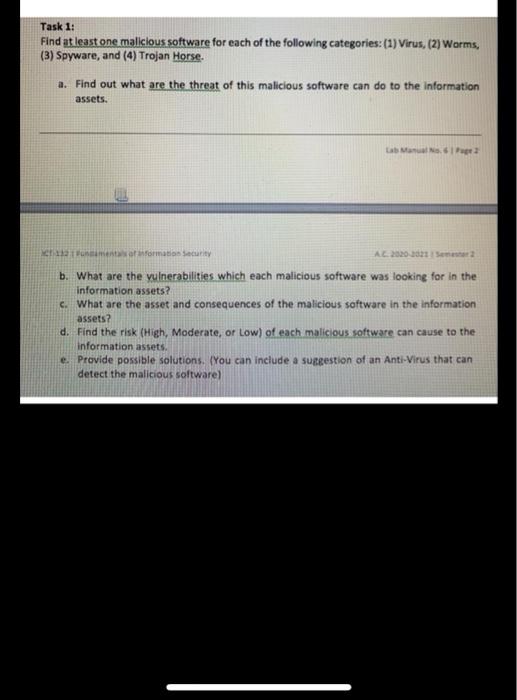

Task 2: Create a Risk Management Plan that corresponds to the research you have made in Task No. 1. Example of Risk Management Plan: Threat Vulnerability Risk Solution Asset and consequences Servers AVEN mat Sym Along Owner 13.00 CH wand PRO Vio w We will M per Nou Seven Servers A Very red Ace in the ES GE D Task 1: Find at least one malicious software for each of the following categories: (1) Virus, (2) Worms, (3) Spyware, and (4) Trojan Horse. a. Find out what are the threat of this malicious software can do to the Information assets. La Mas Para Motormation Security AL 2020 2021 b. What are the vulnerabilities which each malicious software was looking for in the information assets? c. What are the asset and consequences of the malicious software in the information assets? d. Find the risk (High, Moderate, or low) of each malicious software can cause to the information assets, e. Provide possible solutions. You can include a suggestion of an Anti-Virus that can detect the malicious software) Task 2: Create a Risk Management Plan that corresponds to the research you have made in Task No. 1. Example of Risk Management Plan: Threat Vulnerability Risk Solution Asset and consequences Servers AVEN mat Sym Along Owner 13.00 CH wand PRO Vio w We will M per Nou Seven Servers A Very red Ace in the ES GE D Task 1: Find at least one malicious software for each of the following categories: (1) Virus, (2) Worms, (3) Spyware, and (4) Trojan Horse. a. Find out what are the threat of this malicious software can do to the Information assets. La Mas Para Motormation Security AL 2020 2021 b. What are the vulnerabilities which each malicious software was looking for in the information assets? c. What are the asset and consequences of the malicious software in the information assets? d. Find the risk (High, Moderate, or low) of each malicious software can cause to the information assets, e. Provide possible solutions. You can include a suggestion of an Anti-Virus that can detect the malicious software)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


