Question: solve the three tasks Question 1: Find at least one malicious software for each of the following categories: (1) Virus, (2) Worms, (3) Spyware, and
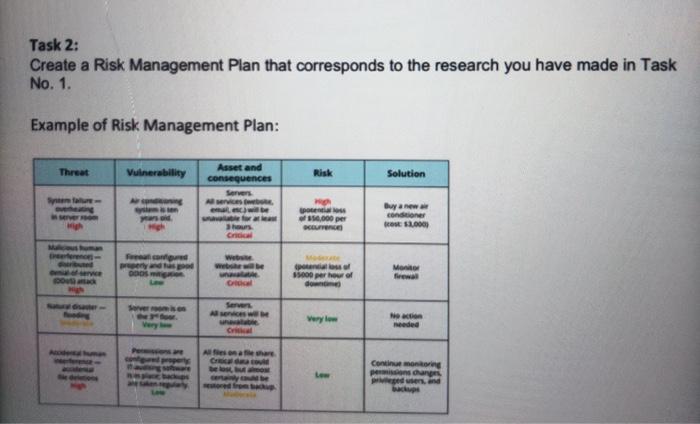
Task 1: Find at least one malicious software for each of the following categories (1) Virus. (2) Worms, (3) Spyware, and (4) Trojan Horse. a. Find out what are the threat of this malicious software can do to the information assets. ICT.132 Fundamentals of information Security AC 2020 2021 Semester 2 b. What are the vulnerabilities which each malicious software was looking for in the information assets? What are the asset and consequences of the malicious software in the information assets? d. Find the risk (High, Moderate, or Low) of each malicious software can cause to the information assets. . Provide possible solutions. You can include a suggestion of an Anti-Virus that can detect the malicious software) Task 2: Create a Risk Management Plan that corresponds to the research you have made in Task No. 1 Example of Risk Management Plan: Task 3: Find at least two real-life situations that happened on the internet. Provide brief information for the following a. Name of the Malicious Software b. The target of the Malicious Software How it was detected d. Damages made by the Malicious Software e. The action made by the victim Note: Provide references for your Lab Report Rubrics: Task 2: Create a Risk Management Plan that corresponds to the research you have made in Task No. 1. Example of Risk Management Plan: Threat Vulnerability Risk Solution Asset and consequences Servers Sema- MON poceni of 50,000 per Currence Buy a new condo cost $2.000 hous Cri FO he posso 5000 per hour of du MO few po Oral Very oper Con monog penge Pred users, and Task 3: Find at least two real-life situations that happened on the internet. Provide brief information for the following: a. Name of the Malicious Software b. The target of the Malicious Software c. How it was detected d. Damages made by the Malicious Software e. The action made by the victim
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


