The first set of questions will be related to the figure below. In the figure, a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
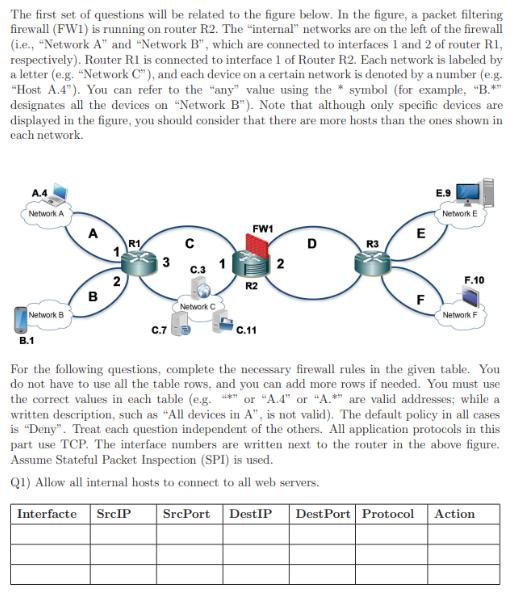
The first set of questions will be related to the figure below. In the figure, a packet filtering firewall (FW1) is running on router R2. The "internal" networks are on the left of the firewall (i.e., "Network A" and "Network B", which are connected to interfaces 1 and 2 of router R1, respectively). Router R1 is connected to interface 1 of Router R2. Each network is labeled by a letter (e.g. "Network C"), and each device on a certain network is denoted by a number (e.g. "Host A.4"). You can refer to the "any" value using the symbol (for example, "B.** designates all the devices on "Network B"). Note that although only specific devices are displayed in the figure, you should consider that there are more hosts than the ones shown in each network. A.4 Network A Network B B.1 A B 2 R1 C.7 Network C FW1 R2 C.11 2 SrcPort DestIP D R3 E Dest Port Protocol F LL E.9 Network E F.10 For the following questions, complete the necessary firewall rules in the given table. You do not have to use all the table rows, and you can add more rows if needed. You must use the correct values in each table (e.g. *" or "A.4" or "A.*" are valid addresses; while a written description, such as "All devices in A", is not valid). The default policy in all cases is "Deny". Treat each question independent of the others. All application protocols in this part use TCP. The interface numbers are written next to the router in the above figure. Assume Stateful Packet Inspection (SPI) is used. Q1) Allow all internal hosts to connect to all web servers. Interfacte SreIP Network F Action The first set of questions will be related to the figure below. In the figure, a packet filtering firewall (FW1) is running on router R2. The "internal" networks are on the left of the firewall (i.e., "Network A" and "Network B", which are connected to interfaces 1 and 2 of router R1, respectively). Router R1 is connected to interface 1 of Router R2. Each network is labeled by a letter (e.g. "Network C"), and each device on a certain network is denoted by a number (e.g. "Host A.4"). You can refer to the "any" value using the symbol (for example, "B.** designates all the devices on "Network B"). Note that although only specific devices are displayed in the figure, you should consider that there are more hosts than the ones shown in each network. A.4 Network A Network B B.1 A B 2 R1 C.7 Network C FW1 R2 C.11 2 SrcPort DestIP D R3 E Dest Port Protocol F LL E.9 Network E F.10 For the following questions, complete the necessary firewall rules in the given table. You do not have to use all the table rows, and you can add more rows if needed. You must use the correct values in each table (e.g. *" or "A.4" or "A.*" are valid addresses; while a written description, such as "All devices in A", is not valid). The default policy in all cases is "Deny". Treat each question independent of the others. All application protocols in this part use TCP. The interface numbers are written next to the router in the above figure. Assume Stateful Packet Inspection (SPI) is used. Q1) Allow all internal hosts to connect to all web servers. Interfacte SreIP Network F Action
Expert Answer:

Related Book For 

Accounting Information Systems
ISBN: 978-0133428537
13th edition
Authors: Marshall B. Romney, Paul J. Steinbart
Posted Date:
Students also viewed these computer network questions
-
A 10.5% coupon bond, semi-annual payments, ten years to maturity is callable in three years at a call price of $1,150. If the bond is selling today for $1120, what is the yield to call ?
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
X-rays of wavelength 0.0973 nm are directed at an unknown crystal. The second diffraction maximum is recorded when the X-rays are directed at an angle of 23.4 relative to the crystal surface. What is...
-
What are the benefits of supply base optimization?
-
On January 1, 2013, Pierce, Inc., purchased 15,000 shares of Marion Company for $435,000, giving Pierce 10 percent ownership of Marion. On January 1, 2014, Pierce purchased an additional 30,000...
-
What are the functions in executing and recording these two classes of transactions and custody of related assets?
-
Allen Products, Inc., wants to do a scenario analysis for the coming year. The pessimistic prediction for sales is $900,000; the most likely amount of sales is $1,125,000; and the optimistic...
-
What are the key principles and techniques of nonviolent communication, and how can they be effectively applied to de-escalate conflicts and foster mutual understanding in high-stakes situations?
-
A cross-flow molecular filtration device equipped with a mesoporous membrane is used to separate the enzyme lysozyme from a fermentation broth, as shown in the figure (right column). Water at...
-
(Adjusting Entries and Financial Statements) Mason Advertising Agency was founded in January 2008. Presented below are adjusted and unadjusted trial balances as of December 31, 2012. FREE ADVERTISING...
-
Write a program that simulates a basic e-commerce shopping cart . The program should include the following functionalities: Add Item: Allow the user to add an item to the cart by specifying the...
-
(b) Fig. 1 illustrates the evolution of TCP's congestion window (cwnd). The unit of time (on the x-axis) is equal to the Round Trip Time (RTT). Reconstruct the sequence of events that explains TCP's...
-
For the mechanism shown, assemble the general dynamic equations of motion in symbolic matrix form? assume point D is the center of gravity of link 3, G the center of gravity of link 2, all masses and...
-
8. For the moving cart and vane in the figure below, let the jet be water of 3 in diameter at 35 ft/s. If the vane angle is 0= 60 and the cart is moving at 15 ft/s, compute the required Fx. P, Vj, Aj...
-
1. A 200 kg chunk of lead falls from a height of 30 m and smashes into a rigid concrete floor. Calculate the increase in the internal energy AU (MJ), assuming that no energy is transferred as heat...
-
The Securities and Exchange Board of India, for the purpose of corporatization and demutualization of a recognized stock exchange issued an order that at least fifty one percent of its equity share...
-
On January 2, 20X3, Sheldon Bass, a professional engineer, moved from Calgary to Edmonton to commence employment with Acco Ltd., a large public corporation. Because of his new employment contract,...
-
Develop a set of tables to implement the integrated REA diagram you developed in Problem 17.6 for the Computer Warehouse in a relational database. Specify a primary key for each table, and suggest at...
-
What internal control procedure(s) would be most effective in preventing the following errors or fraudulent acts? a. An inadvertent data entry error caused an employees wage rate to be overstated in...
-
Ashton Fleming has asked you to document the cash receipts system at S&S. Ashtons narrative of the system follows: Customer payments include cash received at the time of purchase and payments...
-
(a) Among 880 smart phones sold by a retailer, 72 required repairs under the warranty. Estimate the probability that a new phone, which has just been sold, will require repairs under the warranty....
-
A car rental agency has 19 compact cars and 12 intermediate-size cars. If four of the cars are randomly selected for a safety check, what is the probability of getting two of each kind?
-
With reference to Exercise 3.34, suppose that the questionnaire filled in by one of the 150 persons is to be double-checked. If it is chosen in such a way that each questionnaire has a probability of...

Study smarter with the SolutionInn App


