Wheel Bike Shop runs a small but growing bicycle sales and repair business. It has three...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
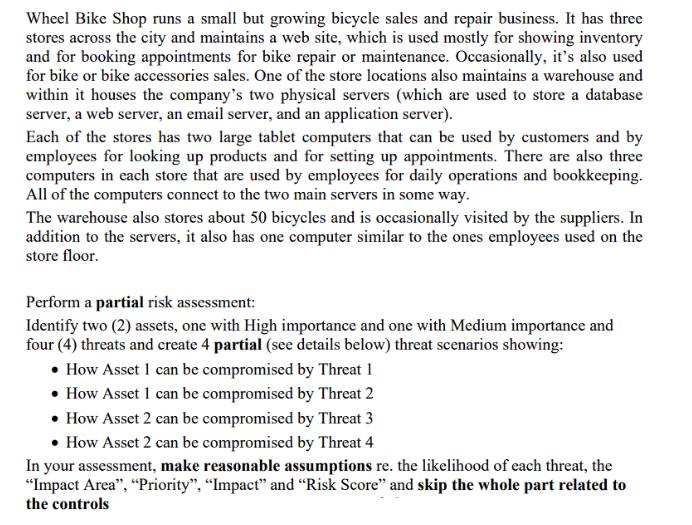
Wheel Bike Shop runs a small but growing bicycle sales and repair business. It has three stores across the city and maintains a web site, which is used mostly for showing inventory and for booking appointments for bike repair or maintenance. Occasionally, it's also used for bike or bike accessories sales. One of the store locations also maintains a warehouse and within it houses the company's two physical servers (which are used to store a database server, a web server, an email server, and an application server). Each of the stores has two large tablet computers that can be used by customers and by employees for looking up products and for setting up appointments. There are also three computers in each store that are used by employees for daily operations and bookkeeping. All of the computers connect to the two main servers in some way. The warehouse also stores about 50 bicycles and is occasionally visited by the suppliers. In addition to the servers, it also has one computer similar to the ones employees used on the store floor. Perform a partial risk assessment: Identify two (2) assets, one with High importance and one with Medium importance and four (4) threats and create 4 partial (see details below) threat scenarios showing: • How Asset I can be compromised by Threat 1 • How Asset 1 can be compromised by Threat 2 • How Asset 2 can be compromised by Threat 3 • How Asset 2 can be compromised by Threat 4 In your assessment, make reasonable assumptions re. the likelihood of each threat, the "Impact Area", "Priority", "Impact" and "Risk Score" and skip the whole part related to the controls Wheel Bike Shop runs a small but growing bicycle sales and repair business. It has three stores across the city and maintains a web site, which is used mostly for showing inventory and for booking appointments for bike repair or maintenance. Occasionally, it's also used for bike or bike accessories sales. One of the store locations also maintains a warehouse and within it houses the company's two physical servers (which are used to store a database server, a web server, an email server, and an application server). Each of the stores has two large tablet computers that can be used by customers and by employees for looking up products and for setting up appointments. There are also three computers in each store that are used by employees for daily operations and bookkeeping. All of the computers connect to the two main servers in some way. The warehouse also stores about 50 bicycles and is occasionally visited by the suppliers. In addition to the servers, it also has one computer similar to the ones employees used on the store floor. Perform a partial risk assessment: Identify two (2) assets, one with High importance and one with Medium importance and four (4) threats and create 4 partial (see details below) threat scenarios showing: • How Asset I can be compromised by Threat 1 • How Asset 1 can be compromised by Threat 2 • How Asset 2 can be compromised by Threat 3 • How Asset 2 can be compromised by Threat 4 In your assessment, make reasonable assumptions re. the likelihood of each threat, the "Impact Area", "Priority", "Impact" and "Risk Score" and skip the whole part related to the controls
Expert Answer:
Answer rating: 100% (QA)
Partial Risk Assessment for Wheel Bike Shop Assets High importance Customer database including customer names addresses contact information and purcha... View the full answer

Related Book For 

Systems Analysis And Design
ISBN: 978-1119496489
7th Edition
Authors: Alan Dennis, Barbara Wixom, Roberta M. Roth
Posted Date:
Students also viewed these computer network questions
-
An outstanding bond is purchased at $9,867.10 with 10 years to maturity, a par value of $10,000 and an annual coupon payment of $800. What is the bond's yield to maturity? A 10-year bond has a par...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Cungs Dress Delivery operates a mail-order business that sells clothes designed for frequent travelers. It had sales of $610,000 in December. Because Cungs Dress Delivery is in the mail order...
-
Using the graphical method of Fig. 8.4, plot the streamlines and potential lines of the flow due to a line source of strength m at (a, 0) plus a line source 3m at (a, 0). What is the flow pattern...
-
Show that the hyperbolas xy = 1 and x2 - y2 = 1 intersect at right angles.
-
Slip for a reciprocating pump is defined as (a) Qa-2th 2th 2th -Qa 2th -Qa Qa-2th (b) (c) (d) Qa 2th Qa
-
Holbrook, a calendar year S corporation, distributes $15,000 cash to its only shareholder, Cody, on December 31. Codys basis in his stock is $20,000, Holbrooks AAA balance is $8,000, and Holbrook...
-
Title IV of Civil Rights Act applied to coaching https://www2.ed.gov/about/offices/list/ocr/docs/interath.html Equal Opportunity In Intercollegiate Athletics: RequirementsUnder Title IX of the...
-
Let X be the winnings of a gambler. Let p(i) = P(X = i) and suppose that Compute the conditional probability that the gambler wins i , i = 1, 2, 3, given that he wins a positive amount. 1/3: p(1) %3...
-
Write a Java program to determine the larger of 2 numbers and the largest of 3 numbers. Each section must use its own method. Method overloading must be used for this exercise. [10] Method for 2...
-
1. Solve. 55/80 + 3/4 = Answer: 3. Solve. 3 MT 4 - 15 + . 5 || 6 2. Solve. 2 17 4. Solve. Answer: 700 8 - 4
-
A real-world topic concerning airports and public relations with local residents. This can center around noise issues, development encroachment, pollution, etc.It can be anything involving a public...
-
Your uncle plans to invest in the tuna fishery for the coming 15 years. The natural growth function of the tuna population (X) is rXln(K/X). The amount of tuna caught during a season (Yt) is a...
-
Graph the NPV of the following cashflows using discount rates between 0 and 250% (by 10%). How many IRRs can you identify? Use Excel's IRR function and the Guess option to identify the IRRs. Under...
-
retail company continuously monitors the thread landscape and identifies a rising trend of point of sale system reaches to medicate the risk they implement end to end encryption for customer payment...
-
Simplify the following expression for p: -)-(-3) -(1- p) = 1 3
-
The graph of an equation is given. (a) Find the intercepts. (b) Indicate whether the graph is symmetric with respect to the x-axis, the y-axis, or the origin. -3 6 -6 3 x
-
Pretend that your mother is a real estate agent and that she has decided to automate her daily tasks by using a laptop computer. Consider her potential hardware and software needs and create a...
-
Draw a level 0 data flow diagram (DFD) for the real estate system in Exercise E, Chapter 4.
-
Ask Jeeves (www.askjeeves.com) is an Internet search engine that uses natural language. Experiment with it and compare it with search engines that use key words.
-
Is an oscillating object in translational equilibrium?
-
How far above Farth's surface must a \(10,000-\mathrm{kg}\) boulder be moved to increase the mass of the Earthboulder system by \(2.50 \mathrm{mg}\) ? Assume the same ratio of energy change to mass...
-
Show that for small displacements the restoring force exerted on part 2 of the displaced string in Figure 15.14 is linearly proportional to the displacement of that part from its equilibrium...

Study smarter with the SolutionInn App


