Question: Write a program to simulate the sending-site FSMs for the Stop-and-Wait protocol (Figure 23.21). Figure 23.21 FSMS for the Stop-and-Wait protocol Sender Request came from
Write a program to simulate the sending-site FSMs for the Stop-and-Wait protocol (Figure 23.21).
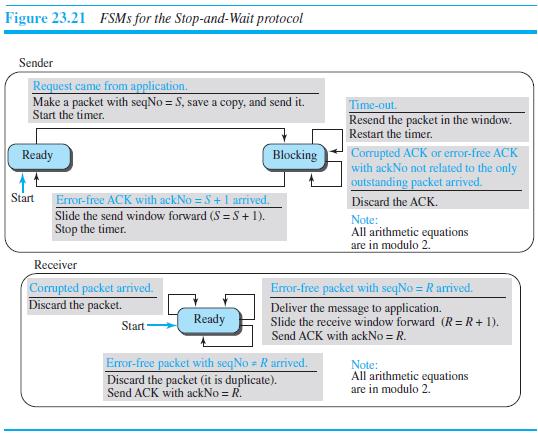
Figure 23.21 FSMS for the Stop-and-Wait protocol Sender Request came from application. Make a packet with seqNo = S, save a copy, and send it. Start the timer. Time-out Resend the packet in the window. Restart the timer. Corrupted ACK or eror-free ACK with ackNo not related to the only outstanding packet arrived. Ready Blocking Start Error-free ACK with ackNo =5+ 1 arrived. Discard the ACK. Slide the send window forward (S =S+1). Stop the timer. Note: All arithmetic equations are in modulo 2. Receiver Corrupted packet arrived. Discard the packet. Error-free packet with seqNo = R arrived. Deliver the message to application. Ready Slide the receive window forward (R= R + 1). Send ACK with ackNo = R. Start Error-free packet with seqNo = R arrived. Discard the packet (it is duplicate). Send ACK with ackNo = R. Note: All arithmetic equations are in modulo 2.
Step by Step Solution
3.33 Rating (162 Votes )
There are 3 Steps involved in it
The second program simulates the StopAndWait protocol at the sender site It ... View full answer

Get step-by-step solutions from verified subject matter experts


