Question: How many 16-byte cache lines are needed to store all 32-bit matrix elements being referenced? Locality is affected by both the reference order and data
How many 16-byte cache lines are needed to store all 32-bit matrix elements being referenced?
Locality is affected by both the reference order and data layout. The same computation can also be written below in Matlab, which differs from C by contiguously storing matrix elements within the same column.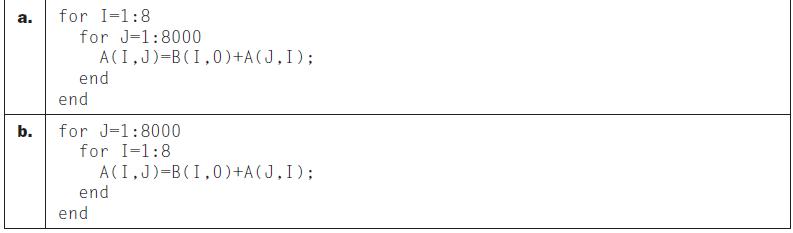
a. b. for I-1:8 for J-1:8000 A(I,J)=B (1,0) +A(J, I); end end for J-1:8000 for I=1:8 A(I,J)=B (1,0) +A(J, I); end end
Step by Step Solution
3.32 Rating (161 Votes )
There are 3 Steps involved in it
To determine the number of 16byte cache lines needed to store all 32bit matrix elements being referenced we need to consider the size of a 32bit eleme... View full answer

Get step-by-step solutions from verified subject matter experts


