Question: If there is no forwarding or hazard detection, insert NOPs to ensure correct execution. This exercise is intended to help you understand the relationship between
If there is no forwarding or hazard detection, insert NOPs to ensure correct execution.
This exercise is intended to help you understand the relationship between forwarding, hazard detection, and ISA design. Problems in this exercise refer to the following sequences of instructions, and assume that it is executed on a 5-stage pipelined datapath: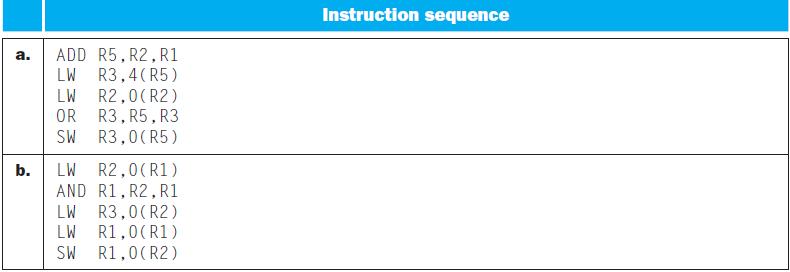
a. b. ADD R5, R2, R1 LW R3,4 (R5) LW R2,0(R2) R3, R5, R3 OR SW R3,0(R5) LW R2,0 (R1) AND R1, R2, R1 LW R3,0(R2) LW R1,0 (R1) R1,0 (R2) SW Instruction sequence
Step by Step Solution
3.47 Rating (154 Votes )
There are 3 Steps involved in it
The question provides two sequences of instructions and asks us to insert NOPs to ensure correct exe... View full answer

Get step-by-step solutions from verified subject matter experts


