Question: Show the execution of method FastExponentiation(5, 12, 13) by constructing a table similar to Table 24.6. Table 24.6. 1|0 8 21 12 6 3 1
Show the execution of method FastExponentiation(5, 12, 13) by constructing a table similar to Table 24.6.
Table 24.6. 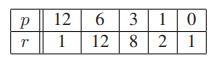
1|0 8 21 12 6 3 1 1 12
Step by Step Solution
3.35 Rating (173 Votes )
There are 3 Steps involved in it
P r ... View full answer

Get step-by-step solutions from verified subject matter experts


