Question: Use double hashing to reimplement the hash table from Figure 11.5. FIGURE 11.5 Implementation of the Table Class Implementation // FILE: Table.java from the package
Use double hashing to reimplement the hash table from Figure 11.5.
![FIGURE 11.5 Implementation of the Table Class Implementation // FILE: Table.java from the package edu.colorado.collections // Documentation is available starting on page 584 or from the Table link at // http://www.cs.colorado.edu/~main/docs/. package edu.colorado.collections; public class Table { private int manyItems; private Object[ ] keys; private Object[ ] data; private boolean[](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/5/5505fb7693e5eeed1605855548802.jpg)
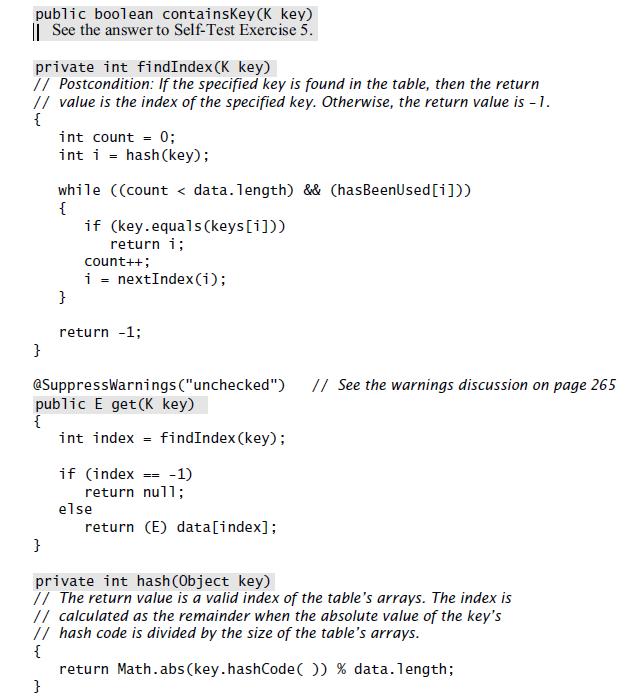
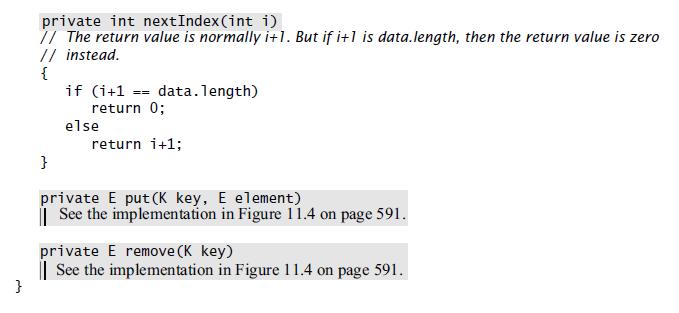
FIGURE 11.5 Implementation of the Table Class Implementation // FILE: Table.java from the package edu.colorado.collections // Documentation is available starting on page 584 or from the Table link at // http://www.cs.colorado.edu/~main/docs/. package edu.colorado.collections; public class Table { private int manyItems; private Object[ ] keys; private Object[ ] data; private boolean[ ] hasBeenUsed; public Table(int capacity) { if (capacity
Step by Step Solution
3.46 Rating (162 Votes )
There are 3 Steps involved in it
Double hashing implementation of the hash table public class HashTable private int size private int ... View full answer

Get step-by-step solutions from verified subject matter experts


