Question: 4- A program has 4 fork statement. When the program runs, how many processes will be created? Explain. 5- What is passed to pipe
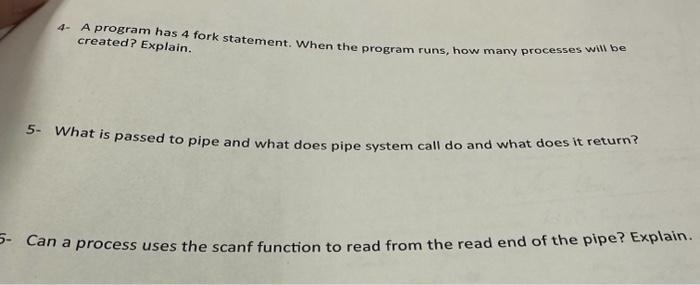
4- A program has 4 fork statement. When the program runs, how many processes will be created? Explain. 5- What is passed to pipe and what does pipe system call do and what does it return? 5- Can a process uses the scanf function to read from the read end of the pipe? Explain.
Step by Step Solution
There are 3 Steps involved in it
4 When a program has 4 fork statements each fork statement creates a new child process Therefore for ... View full answer

Get step-by-step solutions from verified subject matter experts


