Question: 6. Using the Figure below discuss the SYN flood attack. Attacker's computer Sends SYN segments in IP packets to server with modified source addresses Server
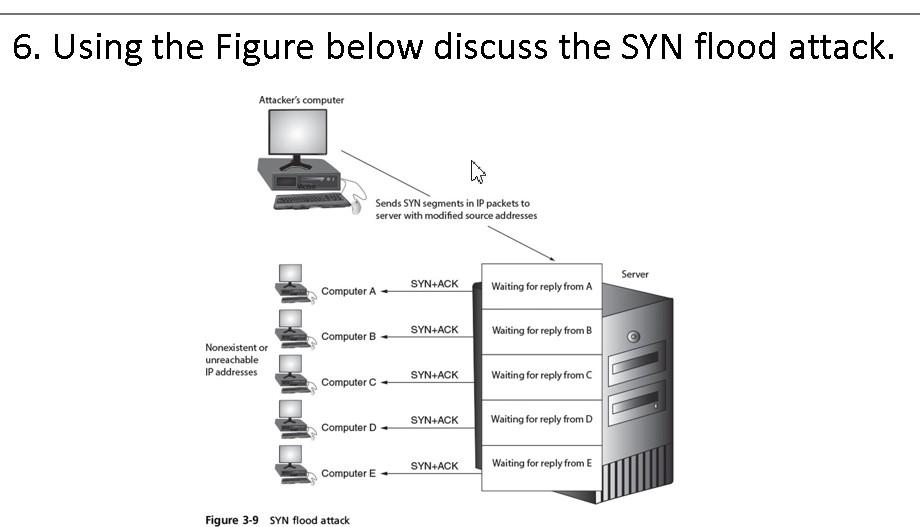
6. Using the Figure below discuss the SYN flood attack. Attacker's computer Sends SYN segments in IP packets to server with modified source addresses Server SYN+ACK Computer A Waiting for reply from A Computer B SYN+ACK Waiting for reply from B Nonexistent or unreachable IP addresses Computer SYN+ACK Waiting for reply from SYN+ACK Computer D Waiting for reply from D Computer E SYN+ACK Waiting for reply from E Figure 3-9 SYN flood attack
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


