Question: A deadlock is a situation in which two computer programs sharing the same resource are effectively preventing each other from accessing the resource, resulting
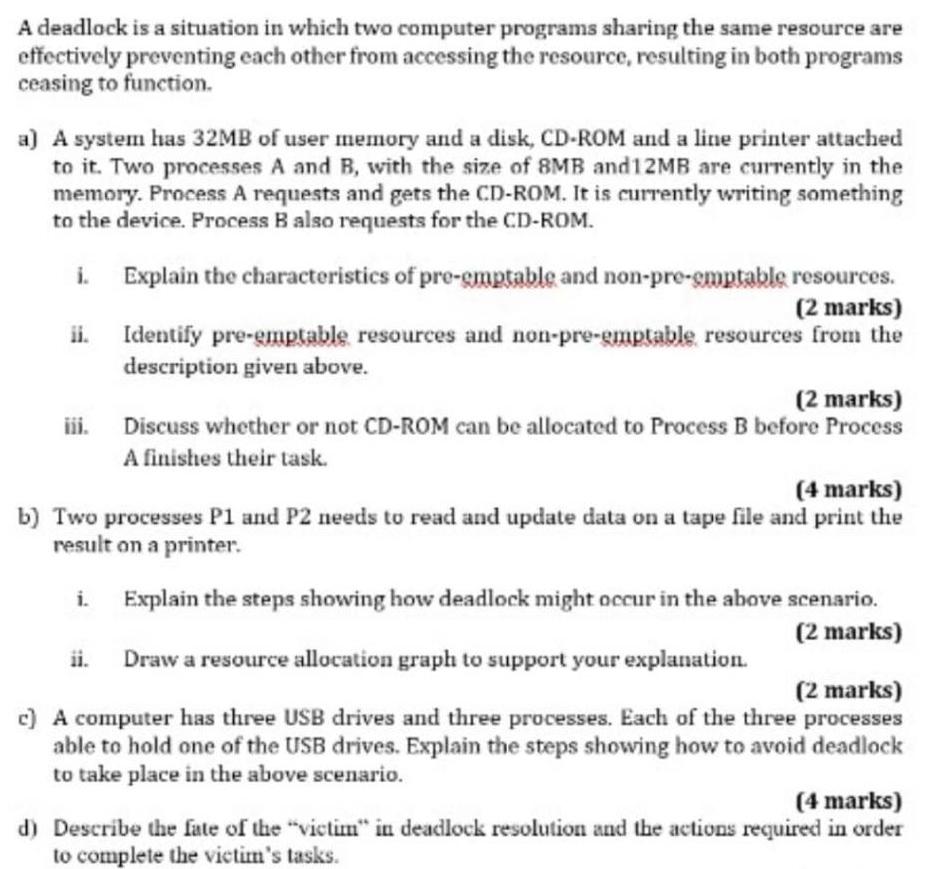
A deadlock is a situation in which two computer programs sharing the same resource are effectively preventing each other from accessing the resource, resulting in both programs ceasing to function. a) A system has 32MB of user memory and a disk, CD-ROM and a line printer attached to it. Two processes A and B, with the size of 8MB and 12MB are currently in the memory. Process A requests and gets the CD-ROM. It is currently writing something to the device. Process B also requests for the CD-ROM. Explain the characteristics of pre-emptable and non-pre-emptable resources. (2 marks) ii. Identify pre-emptable resources and non-pre-emptable resources from the description given above. (2 marks) Discuss whether or not CD-ROM can be allocated to Process B before Process A finishes their task. (4 marks) b) Two processes P1 and P2 needs to read and update data on a tape file and print the result on a printer. i. Explain the steps showing how deadlock might occur in the above scenario. (2 marks) Draw a resource allocation graph to support your explanation. (2 marks) c) A computer has three USB drives and three processes. Each of the three processes able to hold one of the USB drives. Explain the steps showing how to avoid deadlock to take place in the above scenario. (4 marks) d) Describe the fate of the "victim" in deadlock resolution and the actions required in order to complete the victim's tasks.
Step by Step Solution
3.44 Rating (154 Votes )
There are 3 Steps involved in it
SOLUTION a i Preemptable resources These are resources that can be taken away from a process before it has completed its task without causing any harm or inconsistency The process can be paused and th... View full answer

Get step-by-step solutions from verified subject matter experts


