Question: (a) Peter wants to send Alice a text T in the form of binary sequence, T= (0, 0, 1, 0, 1, 0, 0, 1,
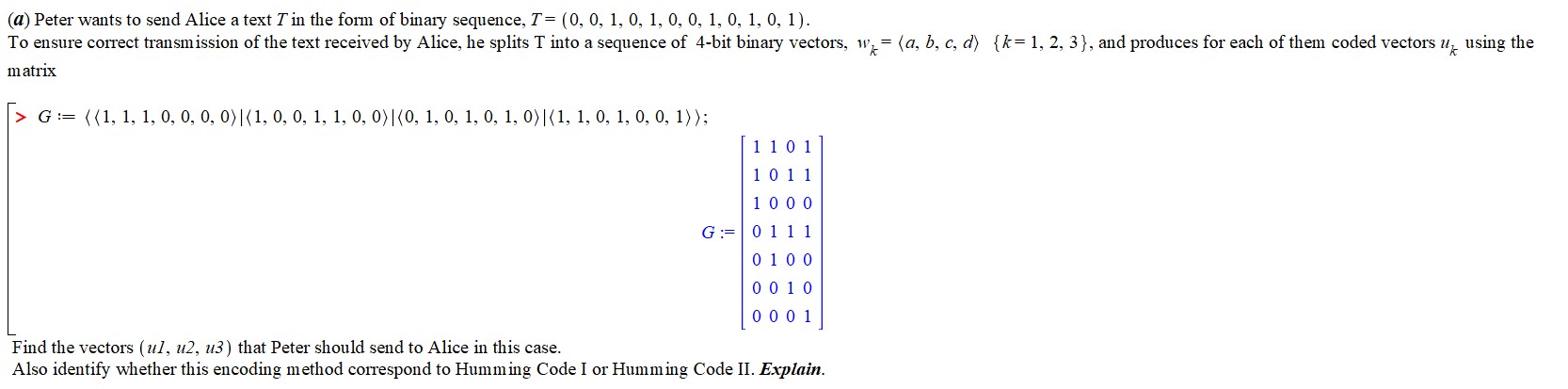
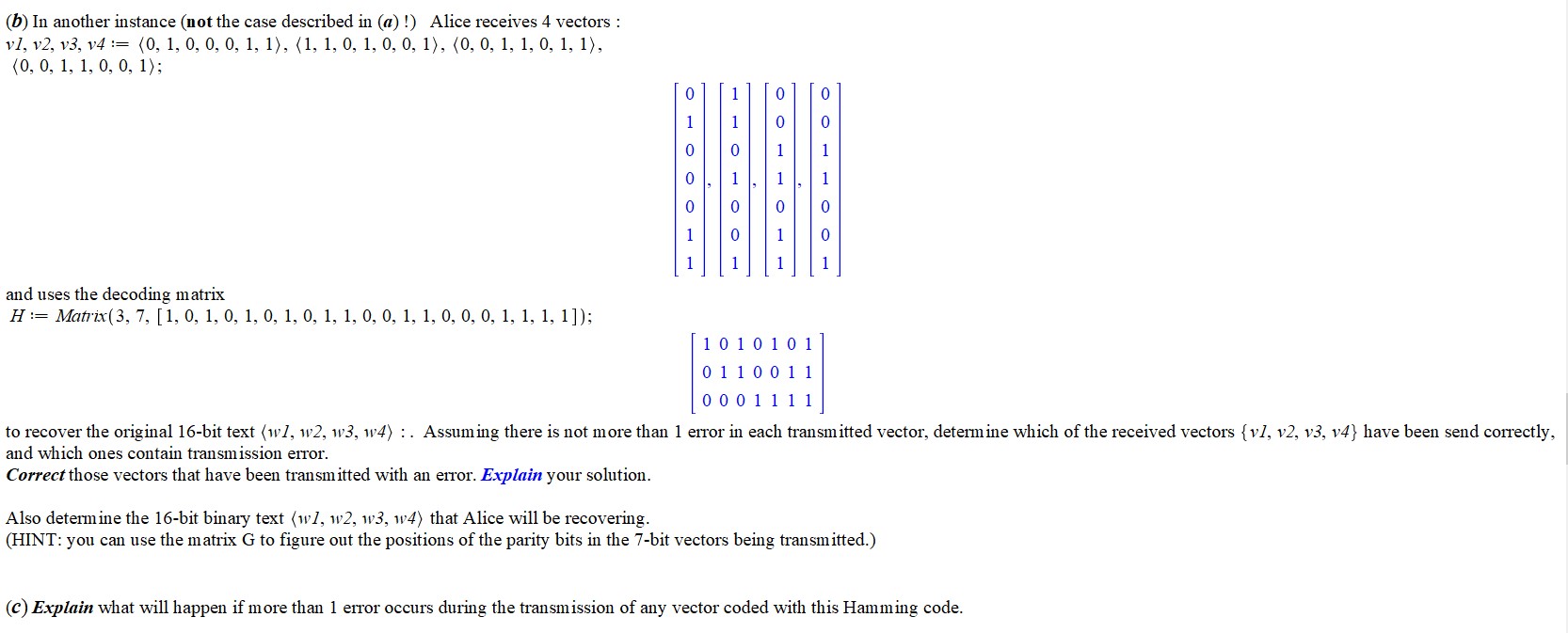
(a) Peter wants to send Alice a text T in the form of binary sequence, T= (0, 0, 1, 0, 1, 0, 0, 1, 0, 1, 0, 1). To ensure correct transmission of the text received by Alice, he splits T into a sequence of 4-bit binary vectors, w= (a, b, c, d) {k=1, 2, 3}, and produces for each of them coded vectors u using the matrix >G ((1, 1, 1, 0, 0, 0, 0)|(1, 0, 0, 1, 1, 0, 0)|(0, 1, 0, 1, 0, 1, 0)|(1, 1, 0, 1, 0, 0, 1)); Find the vectors (ul, u2, u3) that Peter should send to Alice in this case. 1 1 0 1 1 0 1 1 1 0 0 0 G 0111 0 1 0 0 0 0 1 0 0 0 0 1 Also identify whether this encoding method correspond to Humming Code I or Humming Code II. Explain. (b) In another instance (not the case described in (a)!) Alice receives 4 vectors: v1, v2, v3, v4=(0, 1, 0, 0, 0, 1, 1), (1, 1, 0, 1, 0, 0, 1), (0, 0, 1, 1, 0, 1, 1), (0, 0, 1, 1, 0, 0, 1); and uses the decoding matrix H-Matrix(3, 7, [1, 0, 1, 0, 1, 0, 1, 0, 1, 1, 0, 0, 1, 1, 0, 0, 0, 1, 1, 1, 1]); 0 T11 O 0 1 1 19 O 11001 0 1010101 0 1 1 0 0 1 1 0 0 0 1 1 1 1 to recover the original 16-bit text (wl, w2, w3, w4). Assuming there is not more than 1 error in each transmitted vector, determine which of the received vectors {v1, v2, v3, v4} have been send correctly, and which ones contain transmission error. Correct those vectors that have been transmitted with an error. Explain your solution. Also determine the 16-bit binary text (w1, w2, w3, w4) that Alice will be recovering. (HINT: you can use the matrix G to figure out the positions of the parity bits in the 7-bit vectors being transmitted.) (c) Explain what will happen if more than 1 error occurs during the transmission of any vector coded with this Hamming code.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


