Question: answer only. 21 Consider the Java program shown in Figure 10.8. Assume that this is to be compiled to tive code on a machine with
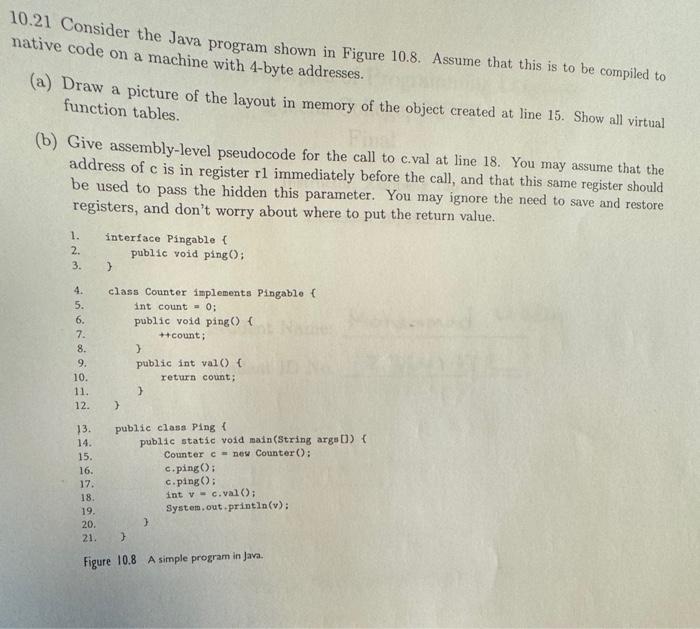
21 Consider the Java program shown in Figure 10.8. Assume that this is to be compiled to tive code on a machine with 4-byte addresses. (a) Draw a picture of the layout in memory of the object created at line 15. Show all virtual function tables. (b) Give assembly-level pseudocode for the call to c.val at line 18. You may assume that the address of c is in register r1 immediately before the call, and that this same register should be used to pass the hidden this parameter. You may ignore the need to save and restore registers, and don't worry about where to put the return value. 1. interface Pingable \{ 2. public void ping(): 3. } 4. class Counter implements Pingable f 5. int count =0; 6. public void ping() f 7. + +count; 8. \} 9. public int val ( f 10. return count; 11. \} 12. \} 13. public clasa Ping 1 14. public static vold main(String args [) f 15. Counter c= new Counter (): 16. c.ping () : 17. c.ping(): 18. int v=c,val(); 19. System, out-printlin(v): 20. \} 21. \} Figure 10.8 A simple program in Jav
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


