Assume you have been recruited to manage a network of security cameras in an office building....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
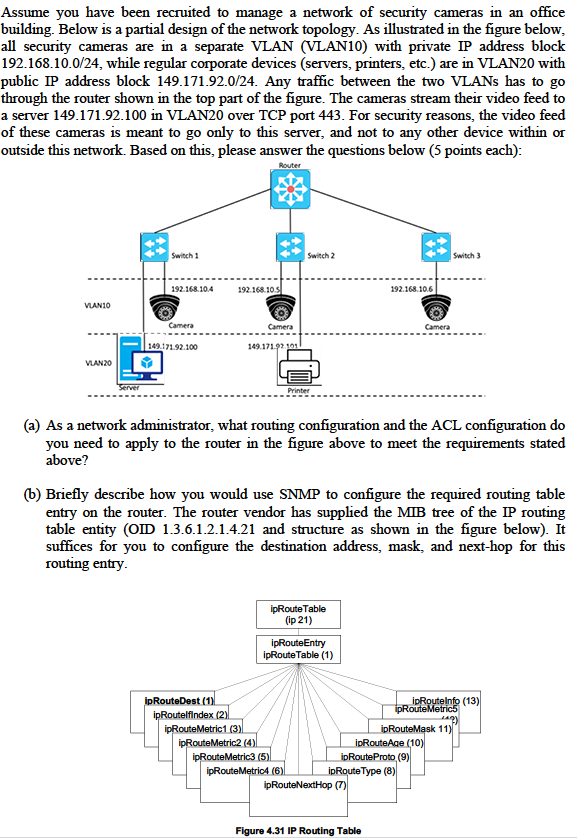
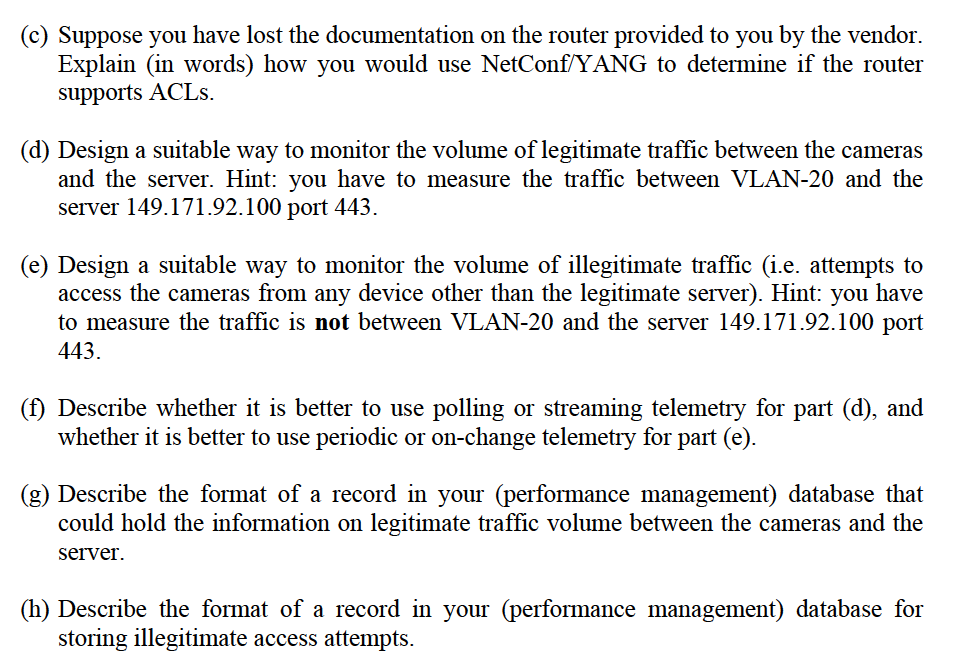
Assume you have been recruited to manage a network of security cameras in an office building. Below is a partial design of the network topology. As illustrated in the figure below, all security cameras are in a separate VLAN (VLAN10) with private IP address block 192.168.10.0/24, while regular corporate devices (servers, printers, etc.) are in VLAN20 with public IP address block 149.171.92.0/24. Any traffic between the two VLANs has to go through the router shown in the top part of the figure. The cameras stream their video feed to a server 149.171.92.100 in VLAN20 over TCP port 443. For security reasons, the video feed of these cameras is meant to go only to this server, and not to any other device within or outside this network. Based on this, please answer the questions below (5 points each): Router VLAN10 VIAN20 Server Switch 1 192.168.10.4 Camera 149.171.92.100 192.168.10.5 ipRouteDest (1) ipRoutelfindex (2) Camera 149.171.92 101 ipRouteMetric1 (3) (a) As a network administrator, what routing configuration and the ACL configuration do you need to apply to the router in the figure above to meet the requirements stated above? ipRouteMetric2 (4) Switch 2 (b) Briefly describe how you would use SNMP to configure the required routing table entry on the router. The router vendor has supplied the MIB tree of the IP routing table entity (OID 1.3.6.1.2.1.4.21 and structure as shown in the figure below). It suffices for you to configure the destination address, mask, and next-hop for this routing entry. Printer ipRouteMetric3 (5) ipRoute Table (ip 21) ipRoute Entry ipRoute Table (1) ipRouteMetric4 (6) 192.168.10.6 ipRouteNextHop (7) Camera ipRouteAge (10) ipRouteProto, (9) Figure 4.31 IP Routing Table ipRoute Type (8) Switch 3 ipRouteInfo (13) ipRouteMetric5 u ipRouteMask 11) (c) Suppose you have lost the documentation on the router provided to you by the vendor. Explain (in words) how you would use NetConf/YANG to determine if the router supports ACLs. (d) Design a suitable way to monitor the volume of legitimate traffic between the cameras and the server. Hint: you have to measure the traffic between VLAN-20 and the server 149.171.92.100 port 443. (e) Design a suitable way to monitor the volume of illegitimate traffic (i.e. attempts to access the cameras from any device other than the legitimate server). Hint: you have to measure the traffic is not between VLAN-20 and the server 149.171.92.100 port 443. (f) Describe whether it is better to use polling or streaming telemetry for part (d), and whether it is better to use periodic or on-change telemetry for part (e). (g) Describe the format of a record in your (performance management) database that could hold the information on legitimate traffic volume between the cameras and the server. (h) Describe the format of a record in your (performance management) database for storing illegitimate access attempts. Assume you have been recruited to manage a network of security cameras in an office building. Below is a partial design of the network topology. As illustrated in the figure below, all security cameras are in a separate VLAN (VLAN10) with private IP address block 192.168.10.0/24, while regular corporate devices (servers, printers, etc.) are in VLAN20 with public IP address block 149.171.92.0/24. Any traffic between the two VLANs has to go through the router shown in the top part of the figure. The cameras stream their video feed to a server 149.171.92.100 in VLAN20 over TCP port 443. For security reasons, the video feed of these cameras is meant to go only to this server, and not to any other device within or outside this network. Based on this, please answer the questions below (5 points each): Router VLAN10 VIAN20 Server Switch 1 192.168.10.4 Camera 149.171.92.100 192.168.10.5 ipRouteDest (1) ipRoutelfindex (2) Camera 149.171.92 101 ipRouteMetric1 (3) (a) As a network administrator, what routing configuration and the ACL configuration do you need to apply to the router in the figure above to meet the requirements stated above? ipRouteMetric2 (4) Switch 2 (b) Briefly describe how you would use SNMP to configure the required routing table entry on the router. The router vendor has supplied the MIB tree of the IP routing table entity (OID 1.3.6.1.2.1.4.21 and structure as shown in the figure below). It suffices for you to configure the destination address, mask, and next-hop for this routing entry. Printer ipRouteMetric3 (5) ipRoute Table (ip 21) ipRoute Entry ipRoute Table (1) ipRouteMetric4 (6) 192.168.10.6 ipRouteNextHop (7) Camera ipRouteAge (10) ipRouteProto, (9) Figure 4.31 IP Routing Table ipRoute Type (8) Switch 3 ipRouteInfo (13) ipRouteMetric5 u ipRouteMask 11) (c) Suppose you have lost the documentation on the router provided to you by the vendor. Explain (in words) how you would use NetConf/YANG to determine if the router supports ACLs. (d) Design a suitable way to monitor the volume of legitimate traffic between the cameras and the server. Hint: you have to measure the traffic between VLAN-20 and the server 149.171.92.100 port 443. (e) Design a suitable way to monitor the volume of illegitimate traffic (i.e. attempts to access the cameras from any device other than the legitimate server). Hint: you have to measure the traffic is not between VLAN-20 and the server 149.171.92.100 port 443. (f) Describe whether it is better to use polling or streaming telemetry for part (d), and whether it is better to use periodic or on-change telemetry for part (e). (g) Describe the format of a record in your (performance management) database that could hold the information on legitimate traffic volume between the cameras and the server. (h) Describe the format of a record in your (performance management) database for storing illegitimate access attempts.
Expert Answer:

Related Book For 

Modern Advanced Accounting In Canada
ISBN: 9781259066481
7th Edition
Authors: Hilton Murray, Herauf Darrell
Posted Date:
Students also viewed these computer network questions
-
Consider the following data set: a. Construct a frequency distribution using classes of 210 up to 0, 0 up to 10, etc. How many of the observations are at least 10 but less than 20? b. Construct a...
-
(a) ABC is a company that manufactures computer desk. The total costs (in RM'000) when x units of computer desk are produced is given by C(x) = 12x 3 - 198x 2 + 1080x Find the level of x that the...
-
Explain the financial investment with the highest and lowest risks available in the marketplace and indicate how you draw your conclusions related to risk level.
-
An adult takes about 12 breaths per minute inhaling roughly 500mL of air with each breath. The molar compositions of the inspired and expired gases are as follows: The inspired gas is at 24?C and 1...
-
The adjusted trial balance of Brompton Bowling Alley at 30 June 2026, the end of the entitys accounting year, follows. Additional data taken into account in the preparation of the above adjusted...
-
In a poll, men and women were asked, When someone yelled or snapped at you at work, how did you want to respond? Twenty percent of the women in the survey said that they felt like crying (Time, April...
-
On the 30th September 2023, you can already an article about a proposed merger relating to ibibi bank. On 1t October you notice that shares of ibibi bank are currently selling at rs. 1000. A)...
-
Consider the following table: Process PO P1 P2 P3 Burst 6 Ops: A. 014 B. 16 Arrival time 0.0 F C. 10 0.5 1.0 2 Priority 8 1.5 1 Calculate Total Waiting Time' for P1 when Priority Algorithm is used? 4
-
You should use the questions listed in each section of Part A of the template to formulate your responses. However, your responses must be in paragraph format , not bullet points or Q & A format....
-
Linux has become a very popular open source operating system. Research and listsome of the advantages and disadvantages of Linux?What is adistro?What are some popular Linuxdistronames? Do you have a...
-
create a mind map of how the various tyles of methods of calculating concentration. Include an example problem with solution and a practical situation in which is method may be required
-
Explain with examples what is meant by project implementation, state and explain in detail the components of project implementation and give 5 importance of project implementation. Explain, Expand...
-
Explain briefly when you would use P&ID drawings in Instrument & Control maintenance.
-
5. Write a C program that computes the number of decimal digits in an entered positive integer number using the function nodec().
-
How many years will it take a $700 balance to grow into $900 in an account earning 5%?
-
When accounting for the acquisition of a non-wholly owned subsidiary, the parent can use entity theory or parent company extension theory to account for the business combination. Access the 2011...
-
On December 31, Year 7, Pepper Company, a public company, agreed to a business combination with Salt Limited, an unrelated private company. Pepper issued 72 of its common shares for all (50) of the...
-
A parent company acquired a 75% interest in a subsidiary company in Year 4. The acquisition price was $1,000,000, made up of cash of $700,000 and the parents common shares with a current market value...
-
Which process would release energy from goldfission or fusion? From carbon? (a) gold: fission; carbon: fusion (b) gold: fusion; carbon: fission (c) gold: fission; carbon: fission (d) gold: fusion;...
-
A certain radioactive element has a half-life of 1 hour. If you start with a 1-g sample of the element at noon, how much of this same element will be left at 3:00 pm? (a) 0.5 g (b) 0.25 g (c) 0.125 g...
-
If an iron nucleus split in two, its fission fragments would have (a) greater mass per nucleon. (b) less mass per nucleon. (c) the same mass per nucleon. (d) either greater or less mass per nucleon.

Study smarter with the SolutionInn App