Question: Consider the Stop-and-Wait protocol. Sender A is communicating with sender B. It takes 5 ms to send a packet from sender A to sender
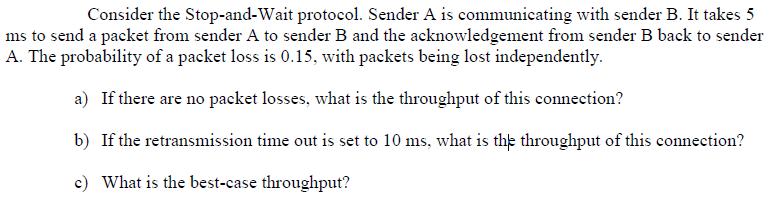
Consider the Stop-and-Wait protocol. Sender A is communicating with sender B. It takes 5 ms to send a packet from sender A to sender B and the acknowledgement from sender B back to sender A. The probability of a packet loss is 0.15, with packets being lost independently. a) If there are no packet losses, what is the throughput of this connection? b) If the retransmission time out is set to 10 ms, what is the throughput of this connection? c) What is the best-case throughput?
Step by Step Solution
There are 3 Steps involved in it
Time taken to send 1 packet 5 ms 5 103 aWithout error ... View full answer

Get step-by-step solutions from verified subject matter experts


