Question: Create a baseline for a computer and protect your server It is essential to set a baseline configuration for each device in order to know
- Create a baseline for a computer and protect your server
- It is essential to set a baseline configuration for each device in order to know how to harden a machine (server or workstation) the best way possible. This should involve recording software, patch, application, and access control analysis versions.
Download and install the Microsoft Baseline Security Analyzer on your host computer, a virtual machine running Windows Client, or Windows Server
- MBSASetup-x64-EN.msiDownload MBSASetup-x64-EN.msi
- Save a copy of your report to submit with your Executive Summary
1. Using a Windows Server VM, harden your server. Consider the following:
- Disable unneeded services.
Most servers have the default install of the operating system, which often contains extraneous services that are not needed for the system to function and that represent a security vulnerability. Therefore, it is critical to remove all unnecessary services from the system. Take a screen shot of what services are on your system and which ones you turned off (or should turn off).
- Ensure all volumes are using NTFS Only
The Windows NTFS file system (NTFS) partitions offer access controls and protections that are not available with the file allocation table (FAT), FAT32, or FAT32x file systems. Make sure that you all partitions on your server are using NTFS. If necessary, use the Convert tool to convert your FAT partitions to NTFS. Take a screen shot showing what type of partitions are on your server.
- Configure Local File/folder permissions.
Another important but often overlooked security procedure is to lock down the file-level permissions for the server. By default, Windows does not apply specific restrictions on any local files or folders; the Everyone group is given full permissions to most of the machine. Remove this group and instead grant access to files and folders using role-based groups based on the least-privilege principle. Every attempt should be made to remove Guest, Everyone and ANONYMOUS LOGON from the user rights lists. With this configuration Windows will be more secure.
- Use a Strong Password on the Administrator Account
In general, longer passwords are stronger than shorter ones, and passwords with several character types (letters, numbers, punctuation marks, and nonprinting ASCII characters generated by using the ALT key and three-digit key codes on the numeric keypad) are stronger than alphabetic or alphanumeric-only passwords.
For maximum protection, ensure the local Administrator account password is at least nine characters long and that it includes at least one punctuation mark or nonprinting ASCII character in the first seven characters. In addition, the Administrator account password should not be synchronized across multiple servers. You should use different passwords on each server to raise the level of security in the workgroup or domain.
Take a screen shot of your password settings.
- Rename the Local Administrator Account
A very simple yet effective procedure that should be a standard part of the hardening process for all servers is to rename the built-in administrator account.
This account is the primary point for attacks, because if successful, the account provides the attacker with virtually unlimited rights. Rename the account, and creat a new user account named Administrator that has not been granted special privileges. You should give this latter account a strong and complex password. You do not need to use this account; it merely serves as a decoy for attack efforts. Do ths at the domain and local computer levels.
The best policy is to rename the local Administrator account to a unique user name that is different on all servers; this minimizes the potential that somehow an attacker will be successful in determining that this new account is the Administrator account in disguise and also managing to crack its password. Because this account is so central to legitimate management tasks, you may view using unique names on every server as unmanageable in practice. In any case, the password for the disguised Administrator account should be unique and different from the other Administrator accounts in the enterprise.
Take a screen grab showing your Local Administrator settings.
- Disable the Guest Account
- By default, the Guest account is disabled on systems running Windows Server. If the Guest account is enabled, you should disable it.
- Set Account Lockout Policy
- For maximum security, enable lockout after 3 to 5 failed attempts, reset the count after not less than 30 minutes, and set the lockout duration to Forever (until admin unlocks). What would you recommend?
- Remove All Unnecessary File Shares
- Look for any file shares that might be configured. Remove all unnecessary file shares on the system to prevent possible information disclosure and to prevent malicious users from using the shares as an entry to the local system.
- Try creating a file share to see what it looks like to the administrator.
- Set Appropriate ACLs on All Necessary File Shares
- By default all users have Full Control permissions on newly creatd file shares. You should set ACLs on all shares that are required on the system so that users have the appropriate share-level access (for example, Everyone = Read).
- Take a screen shot of any file shares you have on your server.
- Enable Audit policies
- Windows audit policy defines what types of events are written in the Security logs of your Windows servers.
- Configure the event Log retention method
- Configure log shipping to SIEM for monitoring
- Install Antivirus Software and Updates
- You should use antivirus software and processes to keep up to date on the latest virus threats. Such protection will only offer value if it is both possible to install and execute code on the target computer; and the protection technology is able to detect and neutralize such efforts. Nevertheless, the ongoing discovery of system shortfalls - such as buffer overruns and the like - that allow a hostile entity to run rogue bits on a computer certainly makes a case for the use of antivirus software.
- How would you determine which antivirus solution to use?
- Install AV and run an initial scan (use free trial versions if available)
Part 2 - Setup a GPO to harden all workstations and servers on your network.
3. Using your Windows Server Active Directory settings, creat a GPO that you would apply corporate wide to lockdown all desktop machines and ensure they are hardened.
4. Apply the following settings within your GPO:
- Enforce password policy
- Set an audit policy
- Creat restricted local groups
- Set permissions on local files
- Enforce firewall settings
- Restrict use of physical inputs and outputs like USB ports
- Enforce windows update settings
- Enable and Enforce Audit logs (define what will be audited from App logs, Syslogs, Security logs)
- Enforce internet browser security
- Enforce Application whitelisting (only allow IE as the browser)
What to submit
An Executive Summary describing what they did in this lab. Describe how you would harden machines in your corporate environment.
- Include your Baseline scan as an appendix to the document.
- Include screenshots of the configurations of the Executive Summary
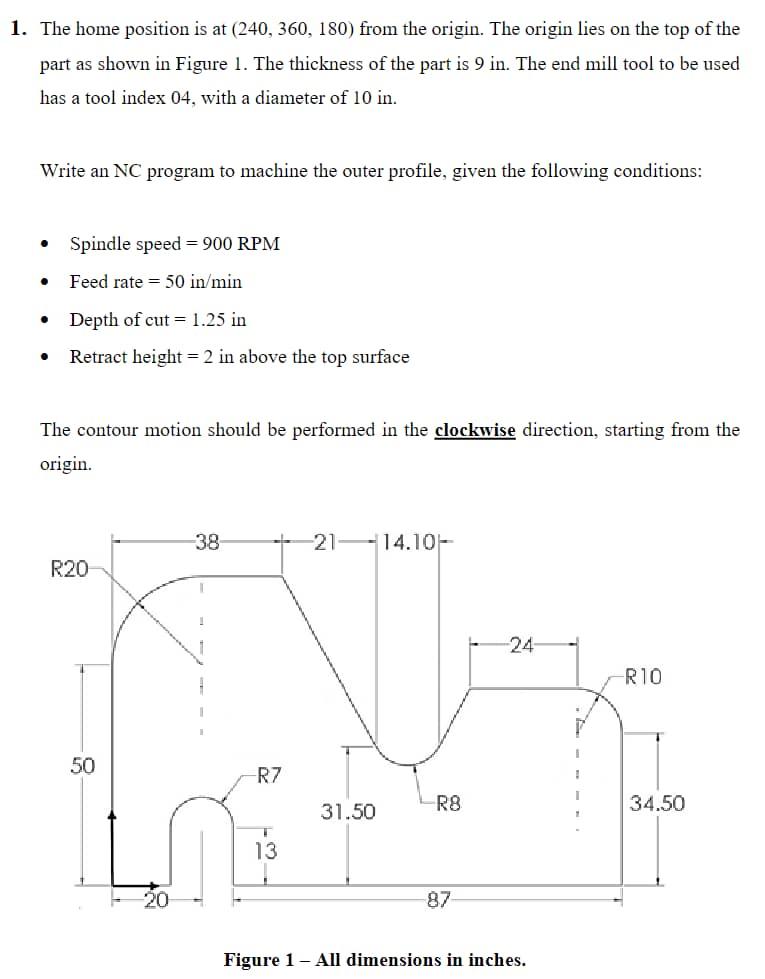
1. The home position is at (240, 360, 180) from the origin. The origin lies on the top of the part as shown in Figure 1. The thickness of the part is 9 in. The end mill tool to be used has a tool index 04, with a diameter of 10 in. Write an NC program to machine the outer profile, given the following conditions: Spindle speed 900 RPM Feed rate=50 in/min Depth of cut = 1.25 in Retract height = 2 in above the top surface The contour motion should be performed in the clockwise direction, starting from the origin. R20 50 -38 -R7 13 -21-14.10- 31.50 R8 87 -24- Figure 1 - All dimensions in inches. I -R10 34.50
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


