Question: Cryptography & Network Security User Authentication. (b) Consider the following proposed authentication protocol between Alice and Bob based on asymmetric encryption which is supposed to
Cryptography & Network Security 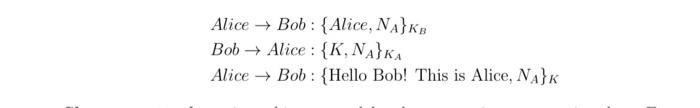
User Authentication.
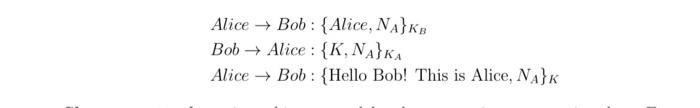
(b) Consider the following proposed authentication protocol between Alice and Bob based on asymmetric encryption which is supposed to establish a shared session key K between the two users. Alices public key is KA and Bobs public key is KB.
Show an attack against this protocol by demonstrating a scenario where Eve can impersonate Alice to Bob (i.e. Bob will think they are talking to Alice when they are in fact talking to Eve). Then provide a fix to the protocol to prevent this attack.
Alice Bob: {Alice, NA}KB Bob Alice : {K, NAHKA Alice + Bob : {Hello Bob! This is Alice, NAHK
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


