Question: Cryptography & Network Security User Authentication. (a) Consider the following proposed authentication protocol between Alice and Bob based on symmetric encryption with a trusted third
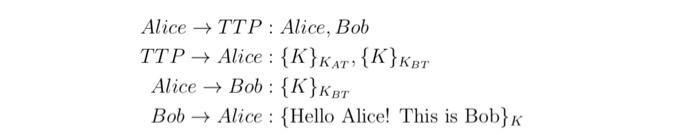
Alice TTP: Alice, Bob TTP + Alice : {K}KAT,{K}Ker Alice + Bob : {K}Ker Bob Alice : {Hello Alice! This is Bob}K
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


