Let (Gen, Enc, Dec) be a private-key encryption scheme that satisfies correctness, and produces ciphertexts that...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
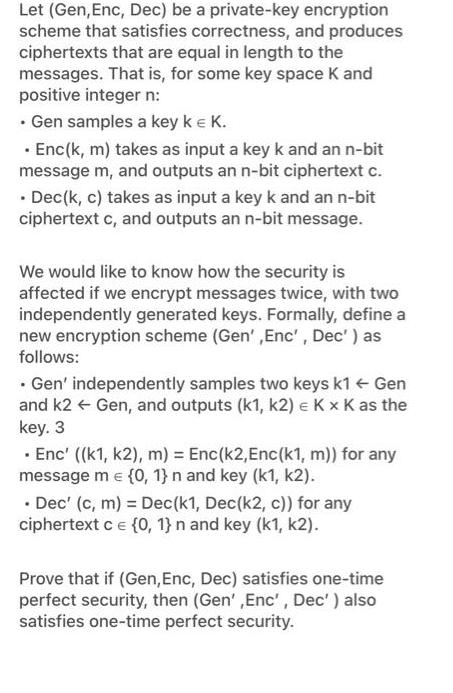
Let (Gen, Enc, Dec) be a private-key encryption scheme that satisfies correctness, and produces ciphertexts that are equal in length to the messages. That is, for some key space K and positive integer n: • Gen samples a key k € K. . Enc(k, m) takes as input a key k and an n-bit message m, and outputs an n-bit ciphertext c. • Dec(k, c) takes as input a key k and an n-bit ciphertext c, and outputs an n-bit message. We would like to know how the security is affected if we encrypt messages twice, with two independently generated keys. Formally, define a new encryption scheme (Gen',Enc', Dec') as follows: • Gen' independently samples two keys k1← Gen and k2 ← Gen, and outputs (k1, k2) € K x K as the key. 3 . • Enc' ((k1, k2), m) = Enc(k2, Enc(k1, m)) for any message m = {0, 1} n and key (k1, k2). . Dec' (c, m) = Dec(k1, Dec(k2, c)) for any ciphertext c = {0, 1} n and key (k1, k2). Prove that if (Gen, Enc, Dec) satisfies one-time perfect security, then (Gen',Enc', Dec') also satisfies one-time perfect security. Let (Gen, Enc, Dec) be a private-key encryption scheme that satisfies correctness, and produces ciphertexts that are equal in length to the messages. That is, for some key space K and positive integer n: • Gen samples a key k € K. . Enc(k, m) takes as input a key k and an n-bit message m, and outputs an n-bit ciphertext c. • Dec(k, c) takes as input a key k and an n-bit ciphertext c, and outputs an n-bit message. We would like to know how the security is affected if we encrypt messages twice, with two independently generated keys. Formally, define a new encryption scheme (Gen',Enc', Dec') as follows: • Gen' independently samples two keys k1← Gen and k2 ← Gen, and outputs (k1, k2) € K x K as the key. 3 . • Enc' ((k1, k2), m) = Enc(k2, Enc(k1, m)) for any message m = {0, 1} n and key (k1, k2). . Dec' (c, m) = Dec(k1, Dec(k2, c)) for any ciphertext c = {0, 1} n and key (k1, k2). Prove that if (Gen, Enc, Dec) satisfies one-time perfect security, then (Gen',Enc', Dec') also satisfies one-time perfect security.
Expert Answer:
Answer rating: 100% (QA)
Definition An encryption scheme Gen EncDec with message spac... View the full answer

Related Book For 

Business
ISBN: 978-1133595854
12th edition
Authors: William M. Pride, Robert J. Hughes, Jack R. Kapoor
Posted Date:
Students also viewed these accounting questions
-
Design, compile and run an object-oriented program to manipulate the required class attributes and operations taking into consideration 10 internal documentation lines. Upload the C++ source code as...
-
11 A gas with a mass of 3 kg has a volume of 3.33 m at a pressure of 135 kPa and temperature 40C. Calculate the gas constant. 12 13 14 Calculate the volume of 2 kg of gas at 1 MPa and 600C if Cy=...
-
An investment of $36,000 was made by a business club. The investment was split into three parts and lasted for one year. The first part of the investment earned8% interest, the second6%, and the...
-
Select the meso compound in the 1 point choices below: * >OH >H rggrr554 CH,OH CH,OH ffffhfghgt
-
Consider a unity negative feedback control system With Verify that the gain margin is co and that the phase margin is 10°. 141 s 12
-
The cost of equipment purchased by Charleston, Inc., on June 1, 2015, is 89,000. It is estimated that the machine will have a 5,000 residual value at the end of its service life. Its service life is...
-
Christopher Boling was seriously injured in 2008 when vapors escaping from a gas can ignited. He filed a products liability claim against the manufacturer. To fund the litigation, Boling entered into...
-
Condensed financial data of Fairchild Company for 2010 and 2009 are presented below. Additional information: During the year, $70 of common stock was issued in exchange for plant assets. No plant...
-
Explain the difference between " management controls ", which are generally the responsibility of the client's Management team and " transaction controls ", which are typically performed by...
-
1. Is Jones correct? That is, using the more complete data set, is it true that Jones has the lowest defect rate overall? Are Joness percentages correct overall (i.e., combining domestic and overseas...
-
Sunshine Sushi, a Japanese restaurant, has the following adjusted trial balance with accounts listed in alphabetical order. For the bank loan, $60,550 is due in 2024. For Notes receivable, $41,500...
-
What is included in the SG&A? Income Statement Account 2018 2019 Revenue 2,500,000 COGS Gross Profit Operating Expenses SG&A Expense Total Operating Expenses Operating Profit (EBIT) Interest Expense...
-
What are the six factors courts may use to determine if the claimed damages are reasonably certain?
-
how does the risk that internal controls over inventory management systems may not be effective influence audit strategy ?Explain
-
Jeff, the owner of a business, withdrew $ 1 0 0 from the business's chequing account for personal use. How would this affect the total equity of his busines?
-
P16.14 Audit Committee Responsibilities A company's audit committee performs duties that are essen- tial to its corporate governance and reporting accuracy. Required Identify the major duties of the...
-
10 s after an electric fan is turned on, it rotates at 300 rev/min. Its average angular acceleration is A. 3/4 rad/s B. C. D. E. 2 rad/s /4 rad/s rad/s /2 rad/s
-
A number of years ago the United Food and Commercial Workers Union organized 800 workers of the 1035 employees at one of the Wilson Brothers food operations in Toronto, Ontario. The employees include...
-
When Chobani decided to pursue distribution in big retail chains, what level of market coverage was it aiming for? Why was this appropriate?
-
Explain the calculation procedure for and significance of each of the following: a. Return of the sales. b. The current ratio. c. Inventory turnover.
-
After mediation failed to help resolve the issues between players and owners, do you think arbitration should have been the next step?Explain your answer.
-
For the probability distribution in Exercise 14, find the sampling distribution of the sample mean for all samples of size \(n=2\). (Hint: The sample means will be the same as given in Figure 3.7,...
-
Minitab can also be used to create a graphical summary of a given variable. The graphical summary can be found by selecting the Stat menu; under Basic Statistics a. Using Minitab, create a graphical...
-
Often we may be interested in comparing the amount of variability between two different data sets. This can be done using the sample coefficient of variation \((C O V)\), which is a percentage that...

Study smarter with the SolutionInn App