Question: In addition to stack-based buffer overflow attacks (i.e., smashing the stack), heap overflows can also be exploited. Execute the following C code, which illustrates a
In addition to stack-based buffer overflow attacks (i.e., smashing the stack), heap overflows can also be exploited.
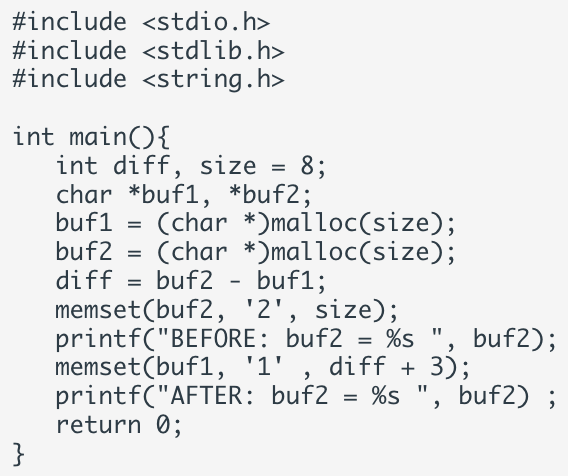
Execute the following C code, which illustrates a heap overflow.
It prints out: BEFORE: buf2 = 22222222 AFTER: buf2 = 11122222
Explain the output, that is, why there's a difference between before & after even the code does not change the content of buf2?
\#include \#include \#include int main()\{ int diff, size =8; char *buf1, buf2; buf1 =( char ) malloc(size); buf2 =( char )malloc(size); diff = buf2 - buf1; memset(buf2, ' 2 ', size); printf("BEFORE: buf2 =% s ", buf2); memset(buf1, '1' , diff +3); printf("AFTER: buf2 =% ", buf2); return 0
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


