Question: Joe has implemented 8 0 2 . 1 x port security on his organization's switches. After configuring the list of MAC addresses that are permitted
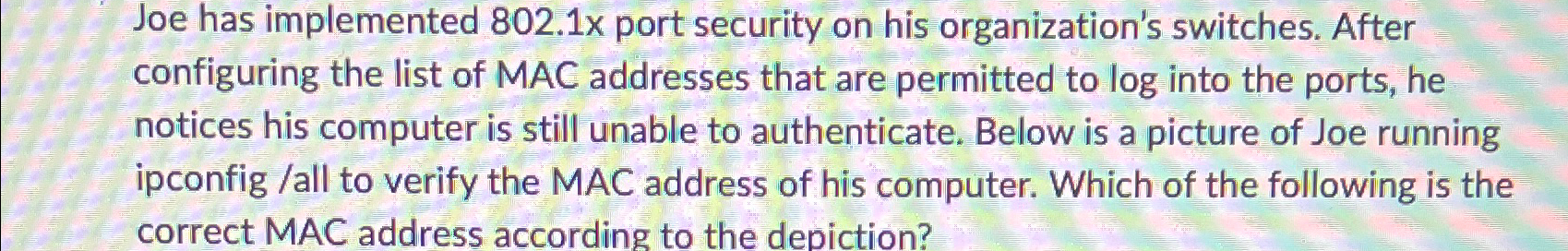
Joe has implemented x port security on his organization's switches. After configuring the list of MAC addresses that are permitted to log into the ports, he notices his computer is still unable to authenticate. Below is a picture of Joe running ipconfig all to verify the MAC address of his computer. Which of the following is the correct MAC address according to the depiction?
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


