Question: Google search Commands examples 5: 1) filetype: Searches for specific filetypes based on the filetype (extension). filetype: pdf filetype:xls 2) Site: Limit your search
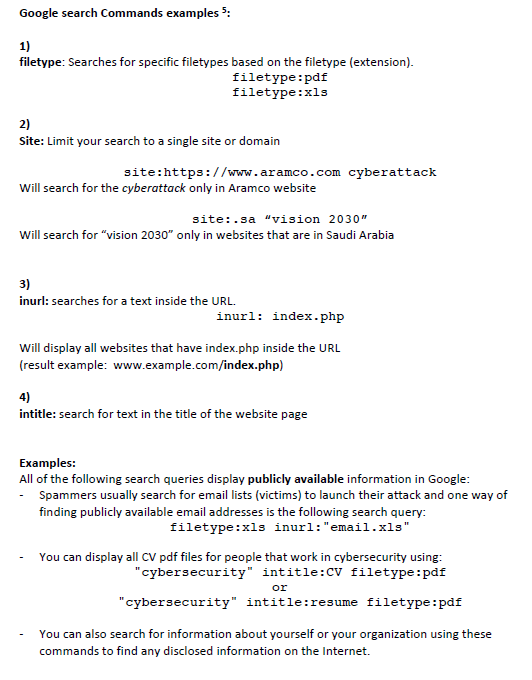
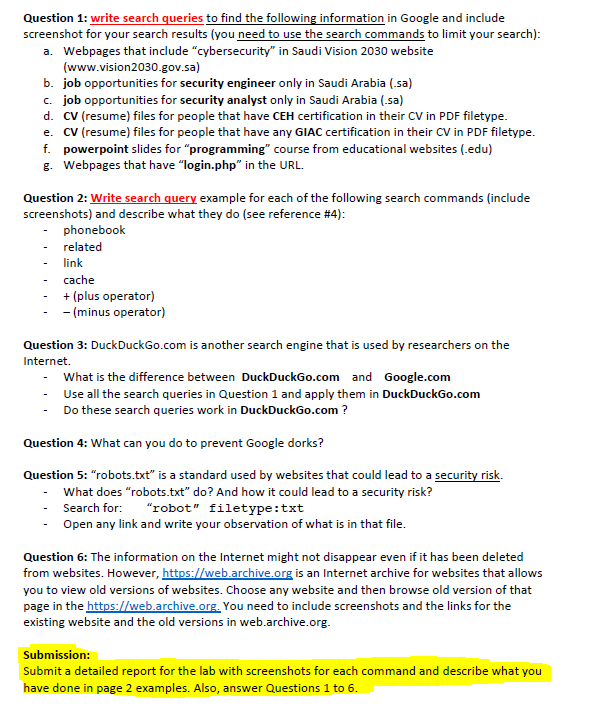
Google search Commands examples 5: 1) filetype: Searches for specific filetypes based on the filetype (extension). filetype: pdf filetype:xls 2) Site: Limit your search to a single site or domain site:https://www.aramco.com cyberattack Will search for the cyberattack only in Aramco website site: .sa "vision 2030" Will search for "vision 2030" only in websites that are in Saudi Arabia 3) inurl: searches for a text inside the URL. inurl: index.php Will display all websites that have index.php inside the URL (result example: www.example.com/index.php) 4) intitle: search for text in the title of the website page Examples: All of the following search queries display publicly available information in Google: - Spammers usually search for email lists (victims) to launch their attack and one way of finding publicly available email addresses is the following search query: filetype:xls inurl: "email.xls" You can display all CV pdf files for people that work in cybersecurity using: "cybersecurity" intitle:CV filetype: pdf or "cybersecurity" intitle: resume filetype: pdf You can also search for information about yourself or your organization using these commands to find any disclosed information on the Internet. Question 1: write search queries to find the following information in Google and include screenshot for your search results (you need to use the search commands to limit your search): a. Webpages that include "cybersecurity" in Saudi Vision 2030 website (www.vision2030.gov.sa) b. job opportunities for security engineer only in Saudi Arabia (.sa) c. job opportunities for security analyst only in Saudi Arabia (.sa) d. CV (resume) files for people that have CEH certification in their CV in PDF filetype. e. CV (resume) files for people that have any GIAC certification in their CV in PDF filetype. f. powerpoint slides for "programming" course from educational websites (.edu) g. Webpages that have "login.php" in the URL. Question 2: Write search query example for each of the following search commands (include screenshots) and describe what they do (see reference #4): phonebook related link cache + (plus operator) -(minus operator) Question 3: DuckDuckGo.com is another search engine that is used by researchers on the Internet. - What is the difference between DuckDuckGo.com and Google.com Use all the search queries in Question 1 and apply them in DuckDuckGo.com Do these search queries work in DuckDuckGo.com ? Question 4: What can you do to prevent Google dorks? Question 5: "robots.txt" is a standard used by websites that could lead to a security risk. What does "robots.txt" do? And how it could lead to a security risk? Search for: "robot" filetype: txt Open any link and write your observation of what is in that file. Question 6: The information on the Internet might not disappear even if it has been deleted from websites. However, https://web.archive.org is an Internet archive for websites that allows you to view old versions of websites. Choose any website and then browse old version of that page in the https://web.archive.org. You need to include screenshots and the links for the existing website and the old versions web.archive.org. Submission: Submit a detailed report for the lab with screenshots for each command and describe what you have done in page 2 examples. Also, answer Questions 1 to 6.
Step by Step Solution
3.36 Rating (152 Votes )
There are 3 Steps involved in it
Q1 a Webpages that include cybersecurity in Saudi Vision 2030 website wwwvision2030govsa Search query sitewwwvision2030govsa cybersecurity Screenshot b Job opportunities for security engineer only in ... View full answer

Get step-by-step solutions from verified subject matter experts


