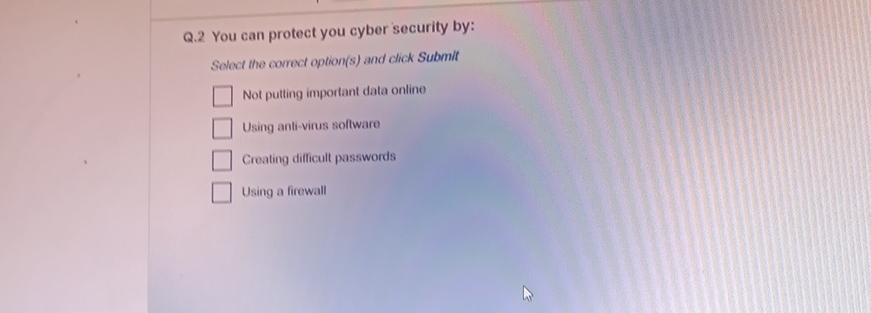
Q.2 You can protect you cyber security by: Select the correct option(s) and click Submit Not...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Q.2 You can protect you cyber security by: Select the correct option(s) and click Submit Not putting important data online Using anti-virus software Creating difficult passwords Using a firewall Q.2 You can protect you cyber security by: Select the correct option(s) and click Submit Not putting important data online Using anti-virus software Creating difficult passwords Using a firewall
Expert Answer:
Answer rating: 100% (QA)
You have provided an image of a multiplechoice question which is about ways to protect cyber securit... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Mrs Anh Thuy is a 43 year old lady admitted following an incidence of blurred vision, numbness down the right side and a sharp pain in her head. A neighbour found her on the ground unable to move or...
-
On January 1, Prescott Corp., issues 6 percent, 15-year bonds payable with a maturity value of $120,000. The bonds sell at 94 and pay interest on January 1 and July 1. Prescott Corp., amortizes any...
-
A firm employing 100 workers has an average absenteeism rate of 4%. On a given day, what is the probability of (a) no workers, (b) one worker, (c) more than six workers being absent?
-
Redesign the fractionator of Example 6.8 for a reflux ratio that is twice the minimum. Determine the diameter of the tower, the height of packing in the stripping and rectifying sections, and the...
-
In the audit of the Worldwide Wholesale Company, you did extensive ratio and trend analysis. No material exceptions were discovered except for the following: 1. Commission expense as a percent of...
-
3. (L)Explain the four terms in the equation below, and why this equation has to be true by definition. Explain the assumption that allows us to use this equation to determine the agricultural...
-
Based on the information contained in these financial statements, compute free cash flow for each company. COLUMBIA SPORTSWEAR COMPANY CONSOLIDATED STATEMENTS OF OPERATIONS (In thousands, except per...
-
Solve the linear, second-order IVP. \(\ddot{x}+4 \dot{x}+4 x=e^{-t}, x(0)=1, \dot{x}(0)=1\)
-
Solve the linear, first-order IVP. \(\dot{u}=(1-u) \cos t, u(0)=\frac{1}{2}\)
-
Solve the linear, first-order IVP. \((t-1) \dot{u}+t u=2 t, u(0)=1\)
-
Solve the linear, first-order IVP. \(\frac{1}{2} \dot{x}+t x=\frac{1}{2} t, x(0)=\frac{1}{3}\)
-
Solve the linear, second-order IVP. \(\ddot{x}+4 x=t, x(0)=0, \dot{x}(0)=1\)
-
New client investigation Assume that we have invited to submit our proposal to provide auditing service for Gaza Community Mental Health Programme (GCMHP) for the year ended December 31, 2019. I have...
-
In each of the following independent cases, document the system using whatever technique(s) your instructor specifies. a. Dreambox Creations (www.dreamboxcreations.com/) in Diamond Bar, California,...
-
Compare and contrast the different positions that are part of an implementation for an information security program. The Chief Information Officer (CIO) is the senior technology officer of an...
-
Comment that a simple action of not including a date on a policy can cause mass confusion for an organization. Stress that without the dates, it will be nearly impossible to determine which version...
-
I. Describe the term separation of duties and why it is important in reducing the risk an organization takes on when limiting the chance an employee will violate information security and break the...
-
One end of a wire is tied to a point A on the ceiling and the other end is tied to a point on a ring of radius \(R\) and negligible mass. The ring therefore hangs from the wire in a vertical plane...
-
A particle moves in a cylindrically symmetric potential \(U(ho, z)\). Use cylindrical coordinates \(ho, \varphi\), and \(z\) to parameterize the space. (a) Write the Lagrangian for an unconstrained...
-
A particle of mass \(m\) slides inside a smooth paraboloid of revolution whose axis of symmetry \(z\) is vertical. The surface is defined by the equation \(z=\alpha ho^{2}\), where \(z\) and \(ho\)...

Study smarter with the SolutionInn App


